Documentation Index
Fetch the complete documentation index at: https://docs.getbifrost.ai/llms.txt
Use this file to discover all available pages before exploring further.
Overview
This guide walks you through configuring Okta as your identity provider for Bifrost Enterprise. After completing this setup, your users will be able to sign in to Bifrost using their Okta credentials, with roles and team memberships automatically synchronized.Prerequisites
- An Okta organization with admin access
- Bifrost Enterprise deployed and accessible
- The redirect URI for your Bifrost instance (e.g.,
https://your-bifrost-domain.com/login) - Ensure you have created all the roles in Bifrost that you are aiming to map to with Okta.
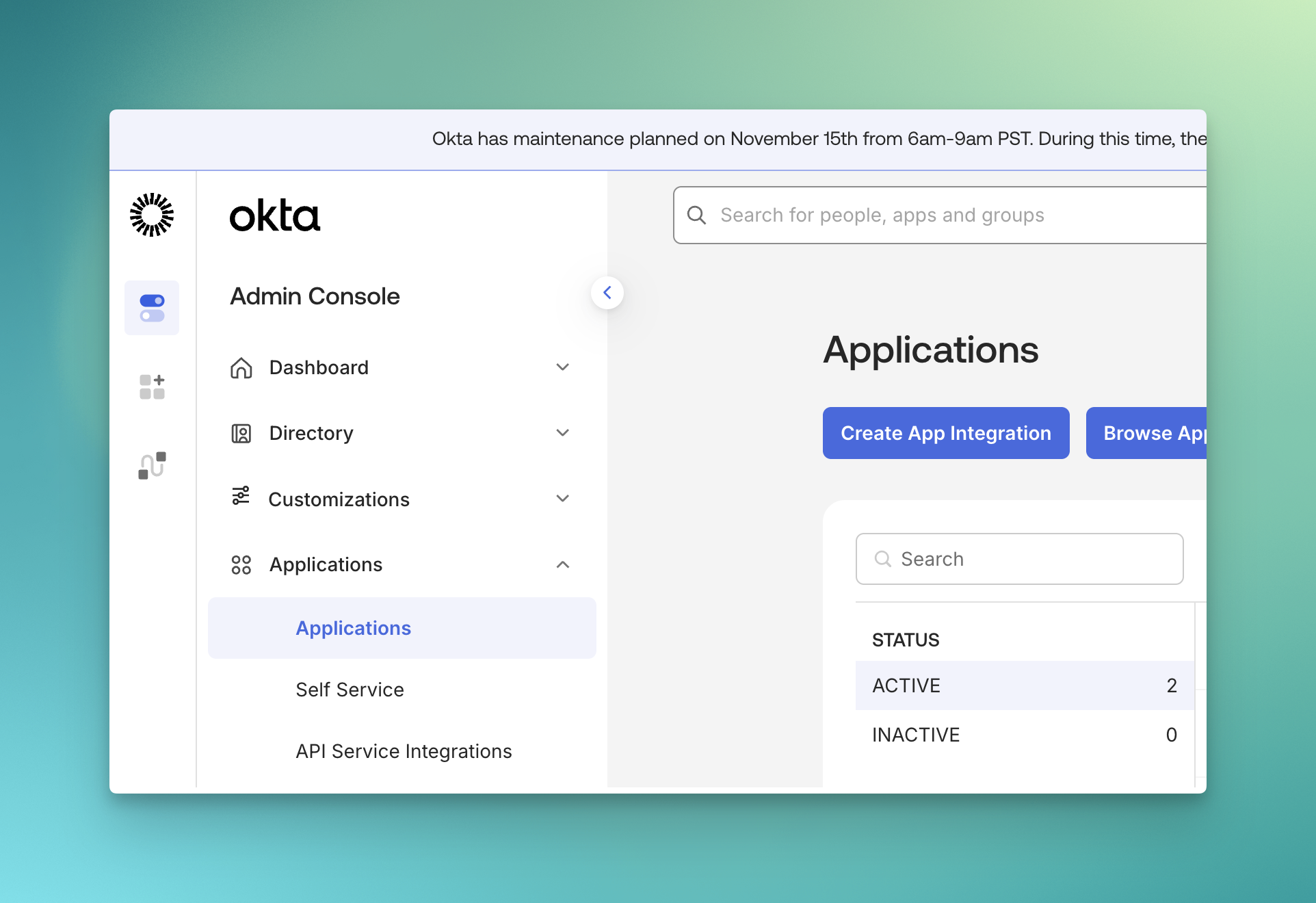
Step 1: Create an OIDC Application
- Log in to the Okta Admin Console
- Navigate to Applications → Applications
- Click Create App Integration
- In the dialog, select:
- Sign-in method: OIDC - OpenID Connect
- Application type: Web Application
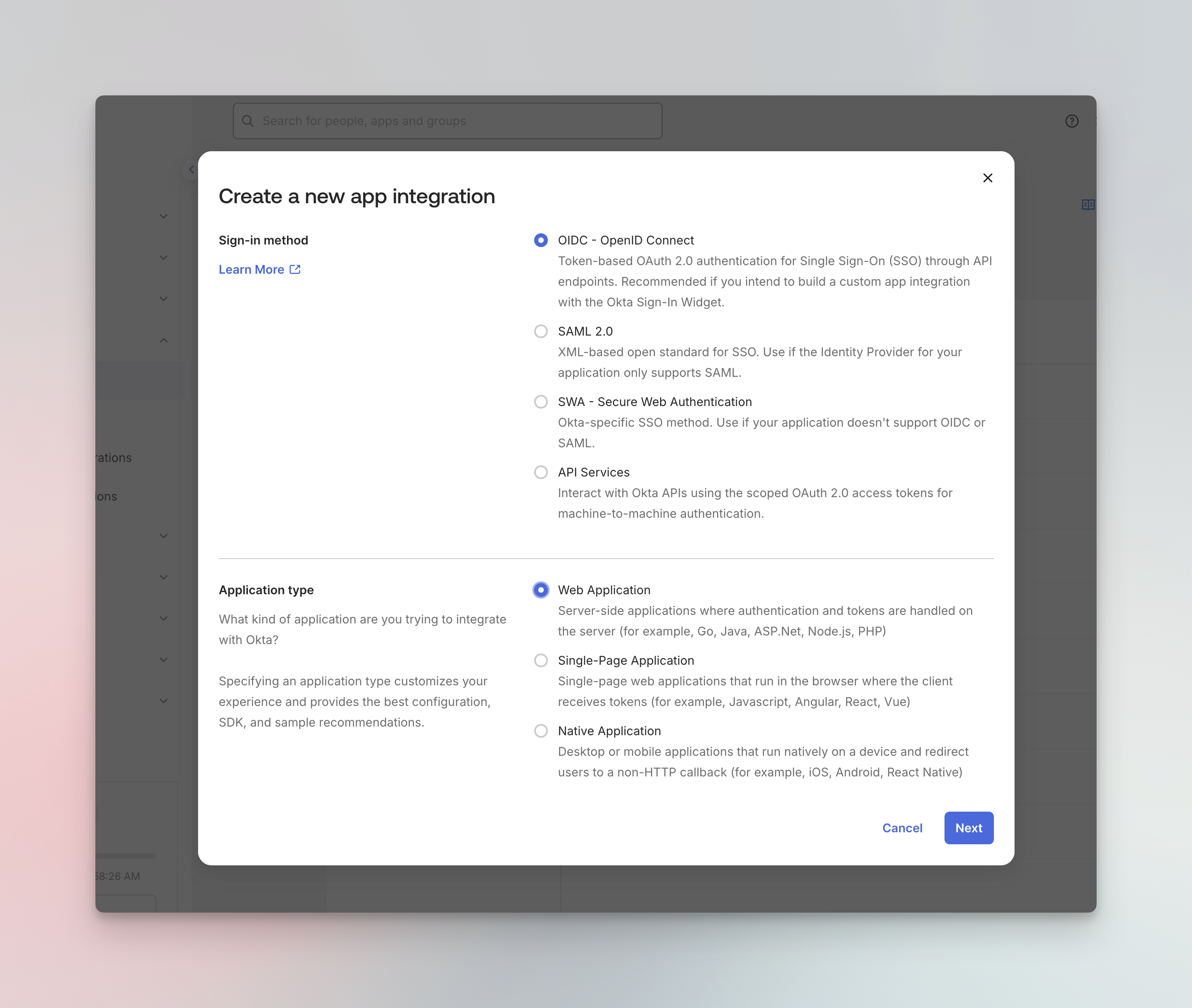
- Click Next to continue
Step 2: Configure Application Settings
Configure the following settings for your application: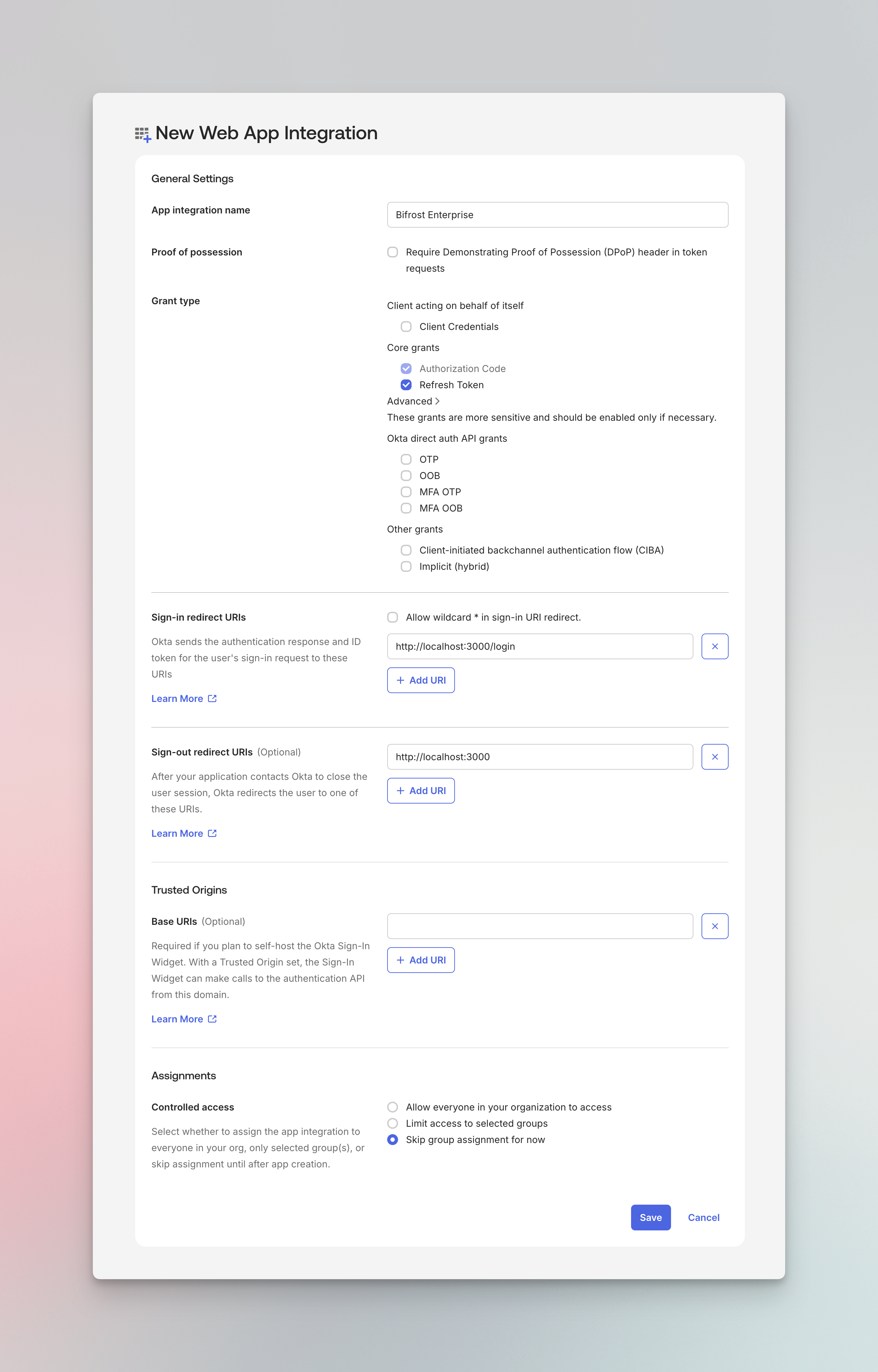
- App integration name:
Bifrost Enterprise - Logo (optional): You can upload the Bifrost logo from https://www.getmaxim.ai/bifrost/bifrost-logo-only.png
- Enable Authorization Code
- Enable Refresh Token
- Add your Bifrost login callback URL:
https://your-bifrost-domain.com/login
- Add your Bifrost base URL:
https://your-bifrost-domain.com
- Choose Skip group assignment for now (we’ll configure this later)
- Click Save to create the application
-
After saving, note down the following from the General tab:
- Client ID
- Client Secret (click to reveal)
Step 3: Create Custom Role Attribute (Optional)
You can map any attribute (include custom roles/groups) to assign roles to users. You can learn more about
RBAC docs.
- Navigate to Directory → Profile Editor
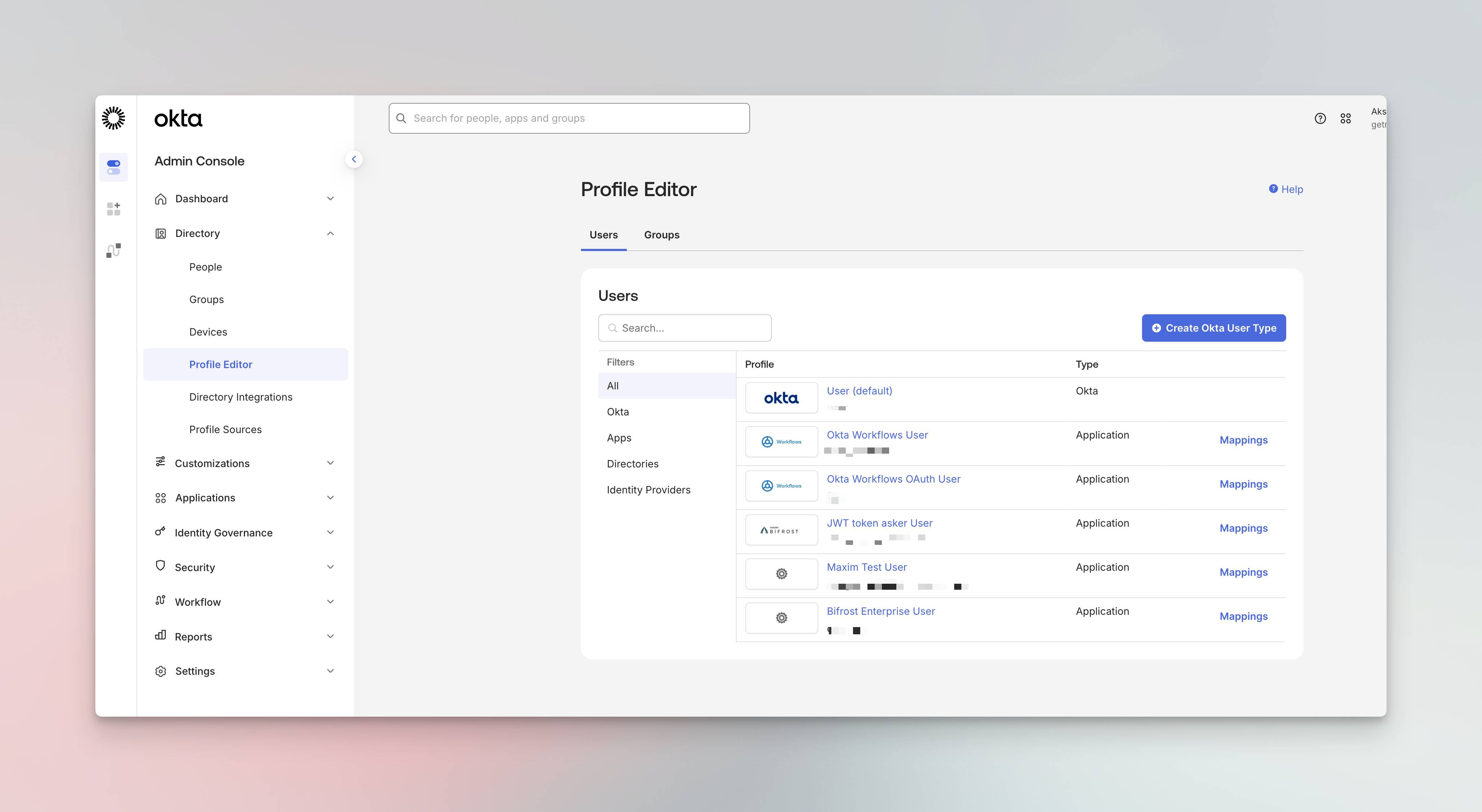
- Click on your application’s user profile (e.g., Bifrost Enterprise User)
- Click Add Attribute
- Configure the attribute:
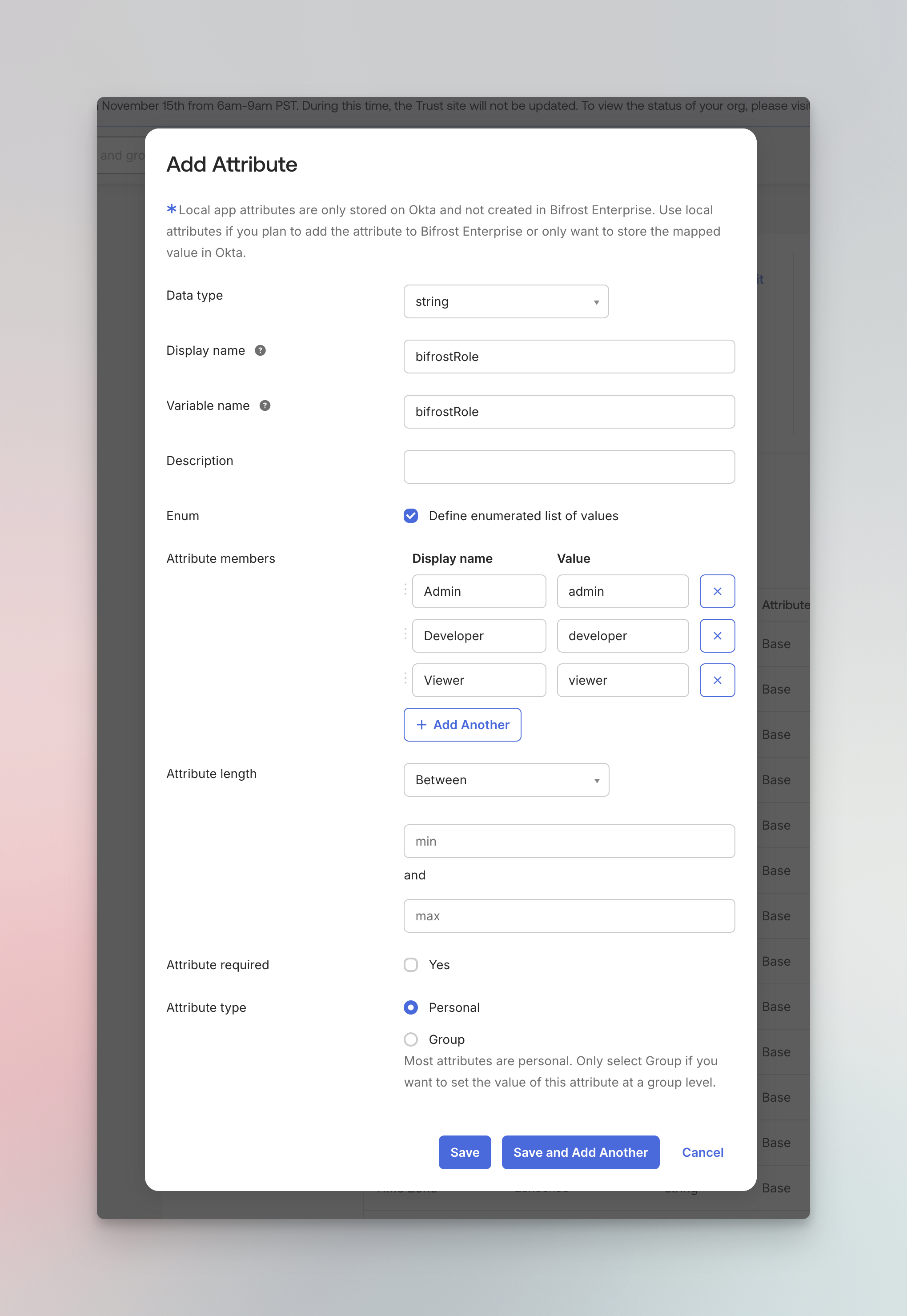
| Field | Value |
|---|---|
| Data type | string |
| Display name | bifrostRole |
| Variable name | bifrostRole |
| Enum | Check “Define enumerated list of values” |
| Attribute members | Admin → admin, Developer → developer, Viewer → viewer |
| Attribute type | Personal |
- Click Save
Step 4: Add Role Claim to Tokens (If you have added custom role attribute)
Configure the authorization server to include the role in the access token.- Navigate to Security → API → Authorization Servers
- Click on your authorization server (e.g., default)
- Go to the Claims tab
- Click Add Claim
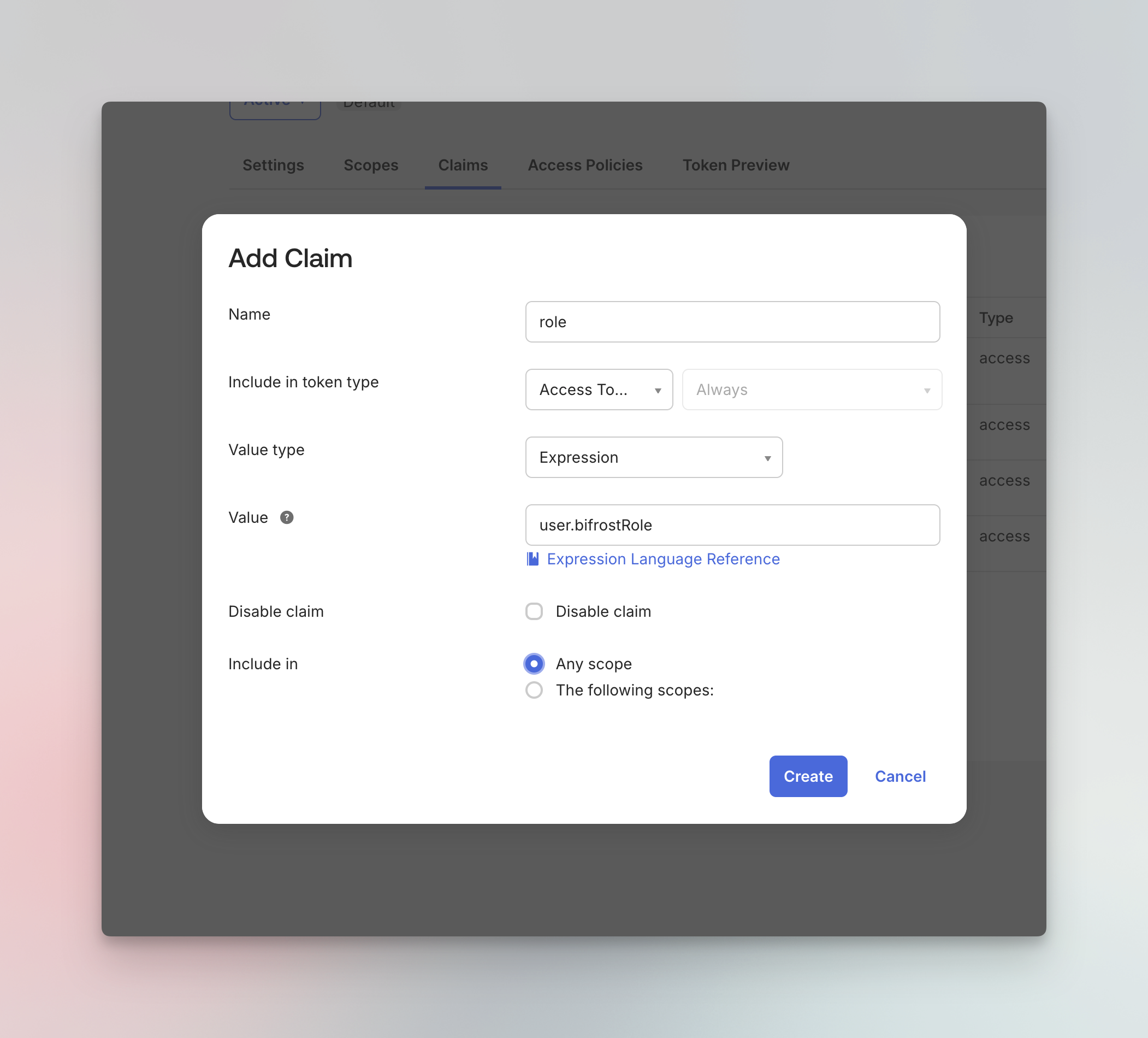
| Field | Value |
|---|---|
| Name | role |
| Include in token type | Access Token, Always |
| Value type | Expression |
| Value | user.bifrostRole |
| Include in | Any scope |
- Click Create
If you named your custom attribute differently, update the Value expression accordingly (e.g.,
user.yourAttributeName).Step 5: Configure Groups
Bifrost can automatically sync Okta groups for two purposes:- Team synchronization - Groups are synced as Bifrost teams
- Role mapping - Groups can be mapped to Bifrost roles (Admin, Developer, Viewer) using Group-to-Role Mappings in the Bifrost UI.
Create Groups in Okta
- Navigate to Directory → Groups
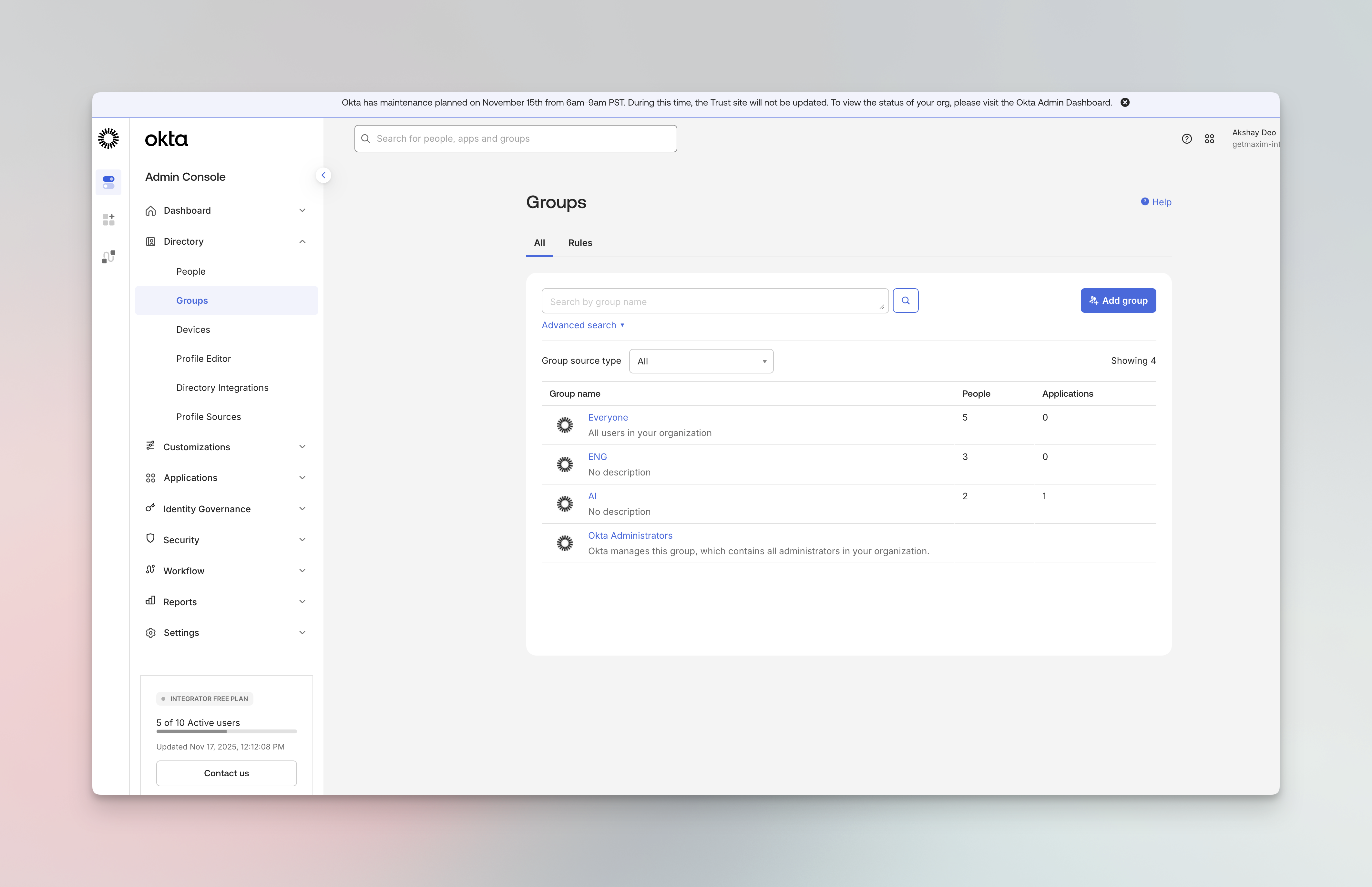
- Click Add group
- Create groups that correspond to your teams or roles (e.g.,
bifrost-staging-admins,bifrost-staging-viewers)
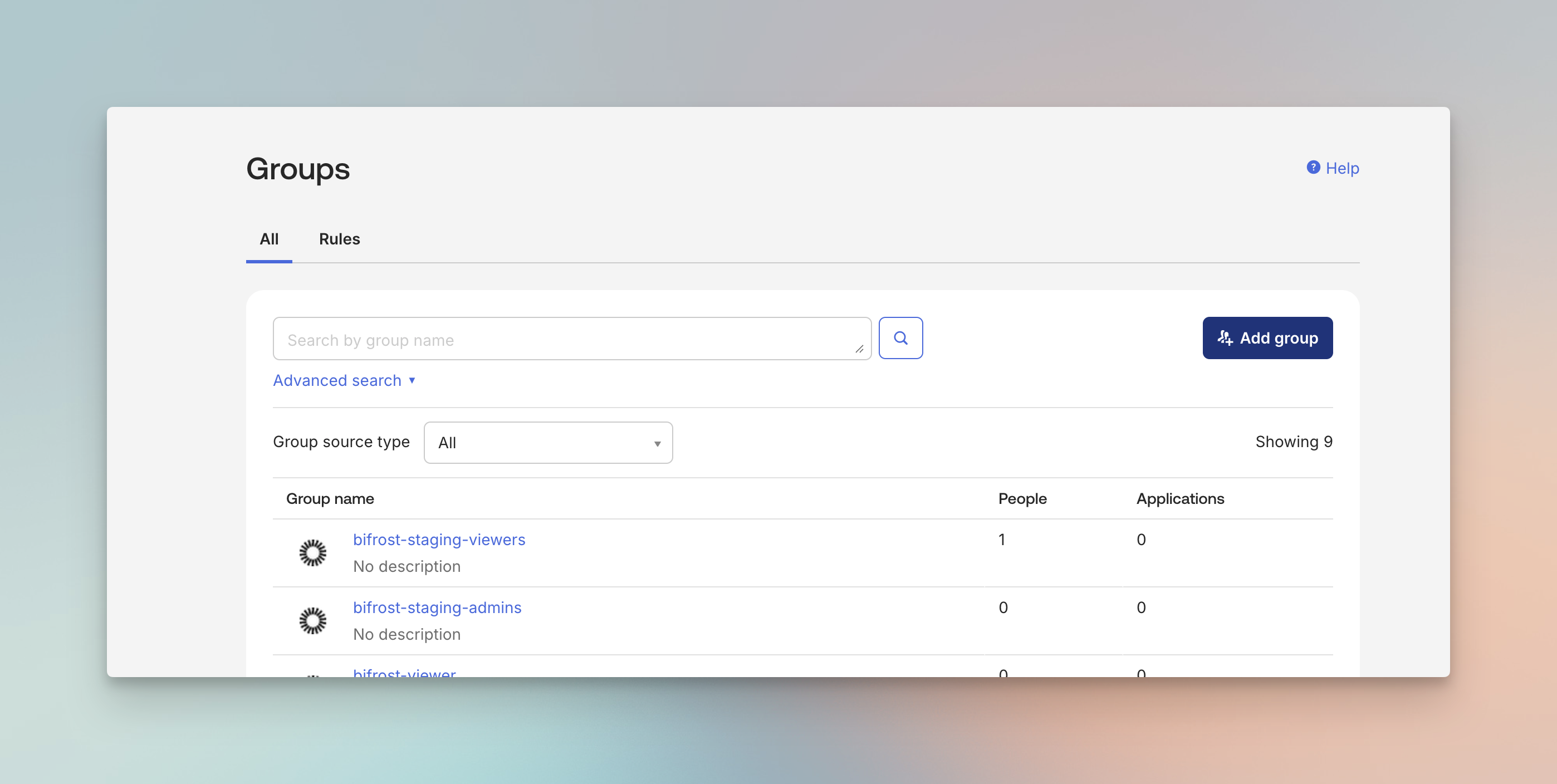
Use a consistent naming convention for your groups. This makes it easier to configure group filters and role mappings
later.
Add Groups Claim to Tokens
This approach adds the groups claim through your authorization server, providing more flexibility for complex configurations.- Navigate to Security → API → Authorization Servers
- Select your authorization server (e.g., default)
- Go to the Claims tab
- Click Add Claim
| Field | Value |
|---|---|
| Name | groups |
| Include in token type | ID Token, Always |
| Value type | Groups |
| Filter | Matches regex: .* (or specify a prefix like bifrost-.*) |
| Include in | Any scope |
- Click Create
Step 6: Assign Users to the Application
- Navigate to your application’s Assignments tab
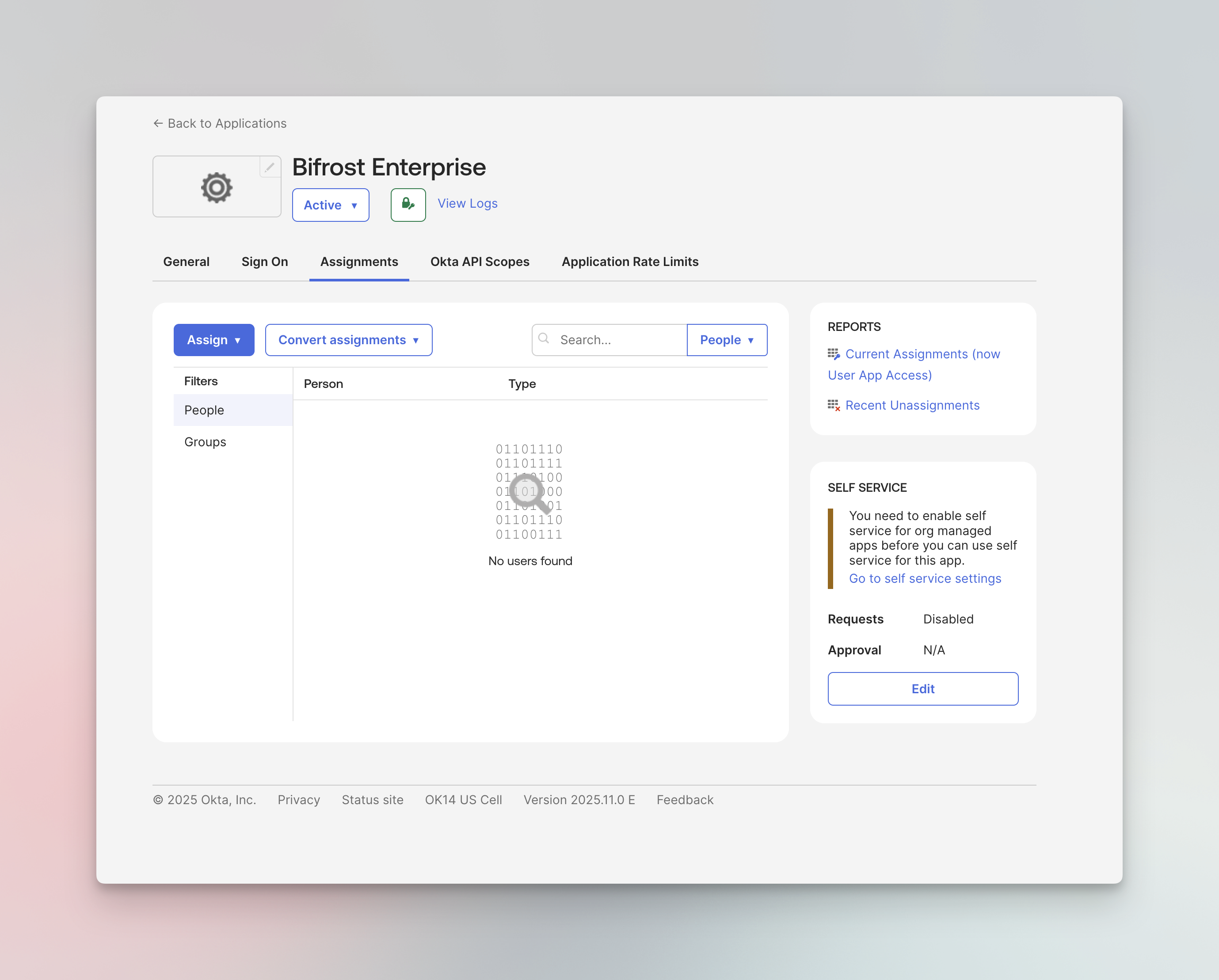
- Click Assign → Assign to People or Assign to Groups
For Assigning Roles (If step 3 and step 4 are followed)
For each user, set their bifrostRole (if you are planning to do role-level mapping):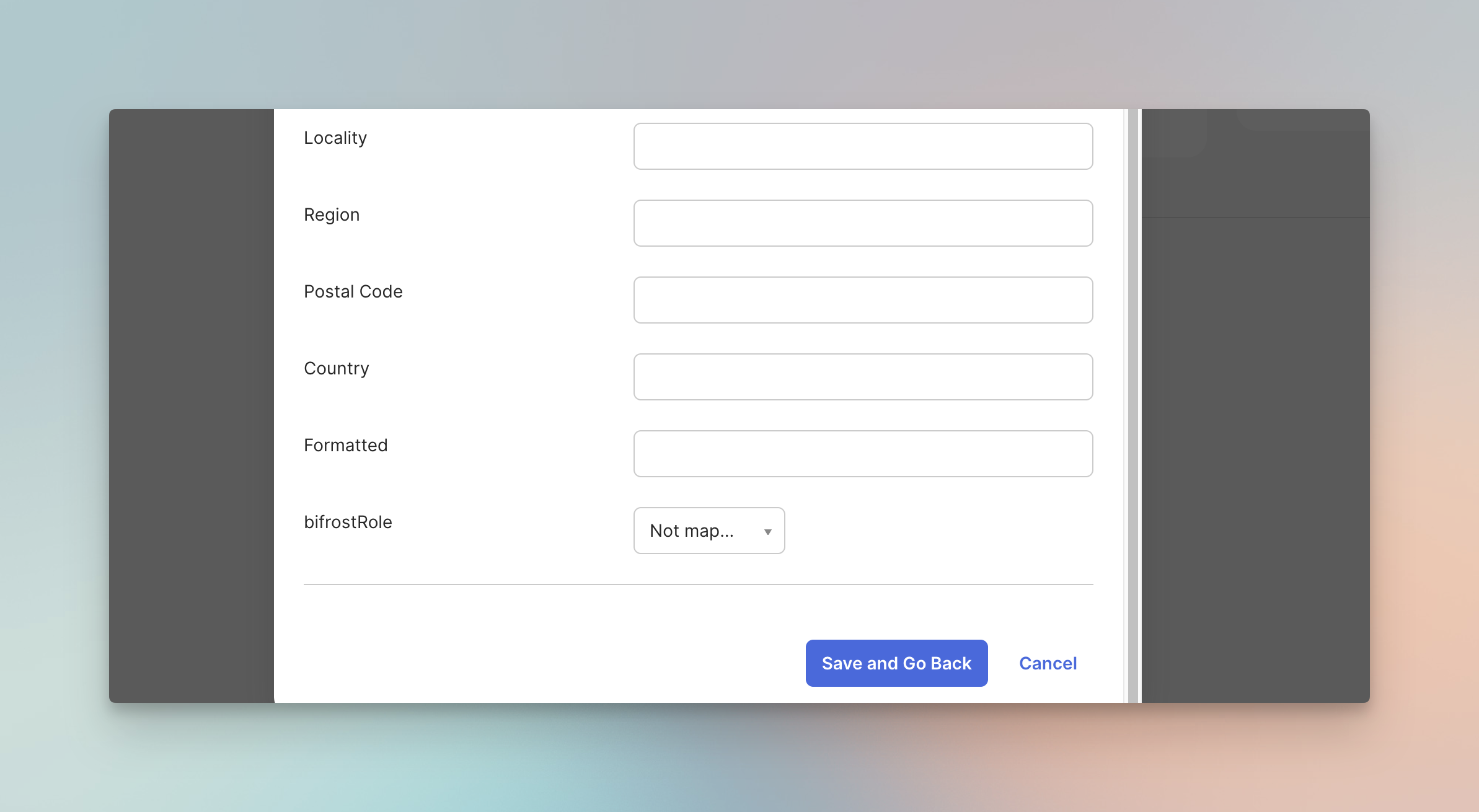
- Click Save and Go Back
Step 7: Create API token for bulk user and team sync
To create an API token, navigate to Security → API → Tokens.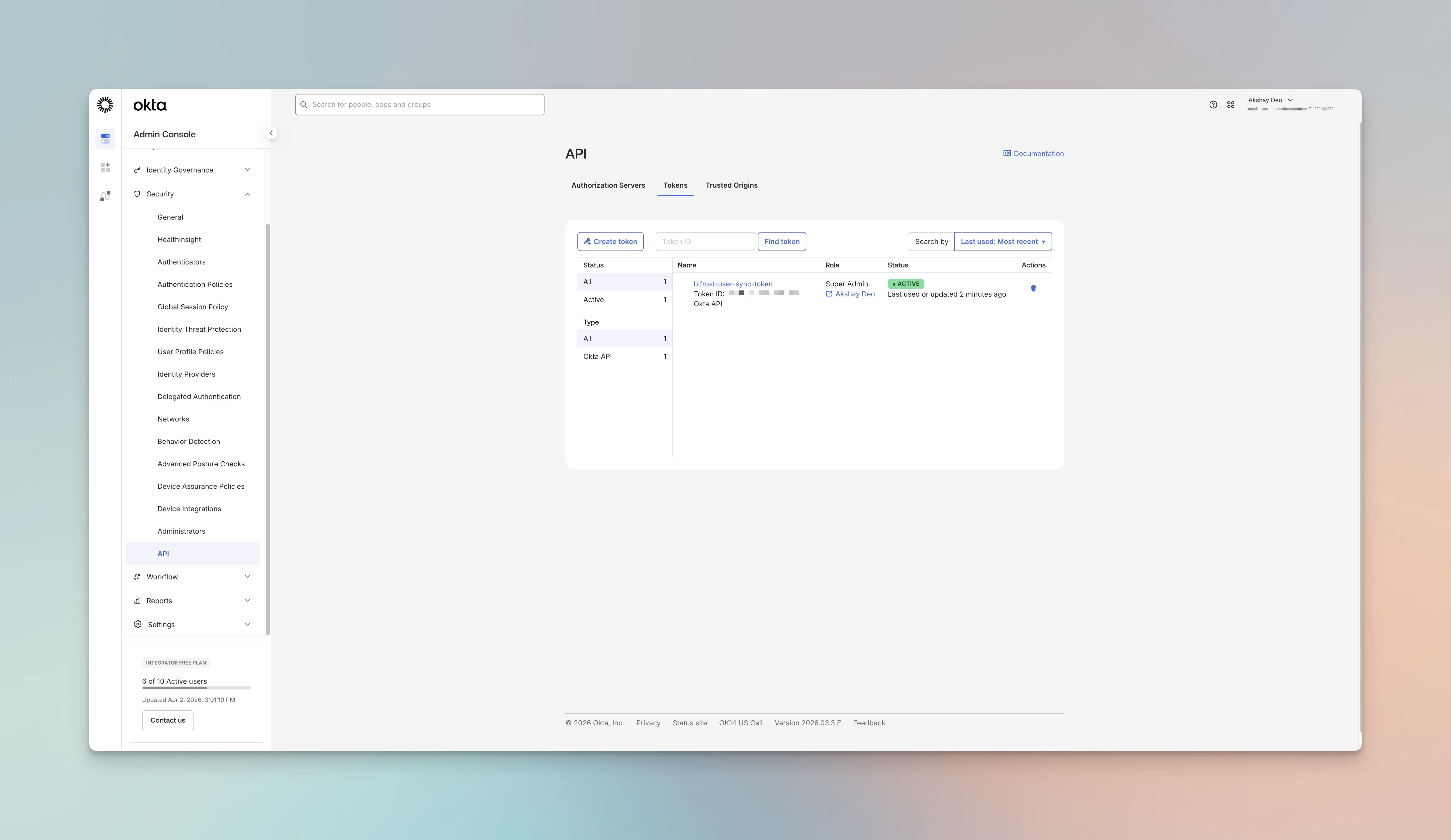
- Click on “Create token”
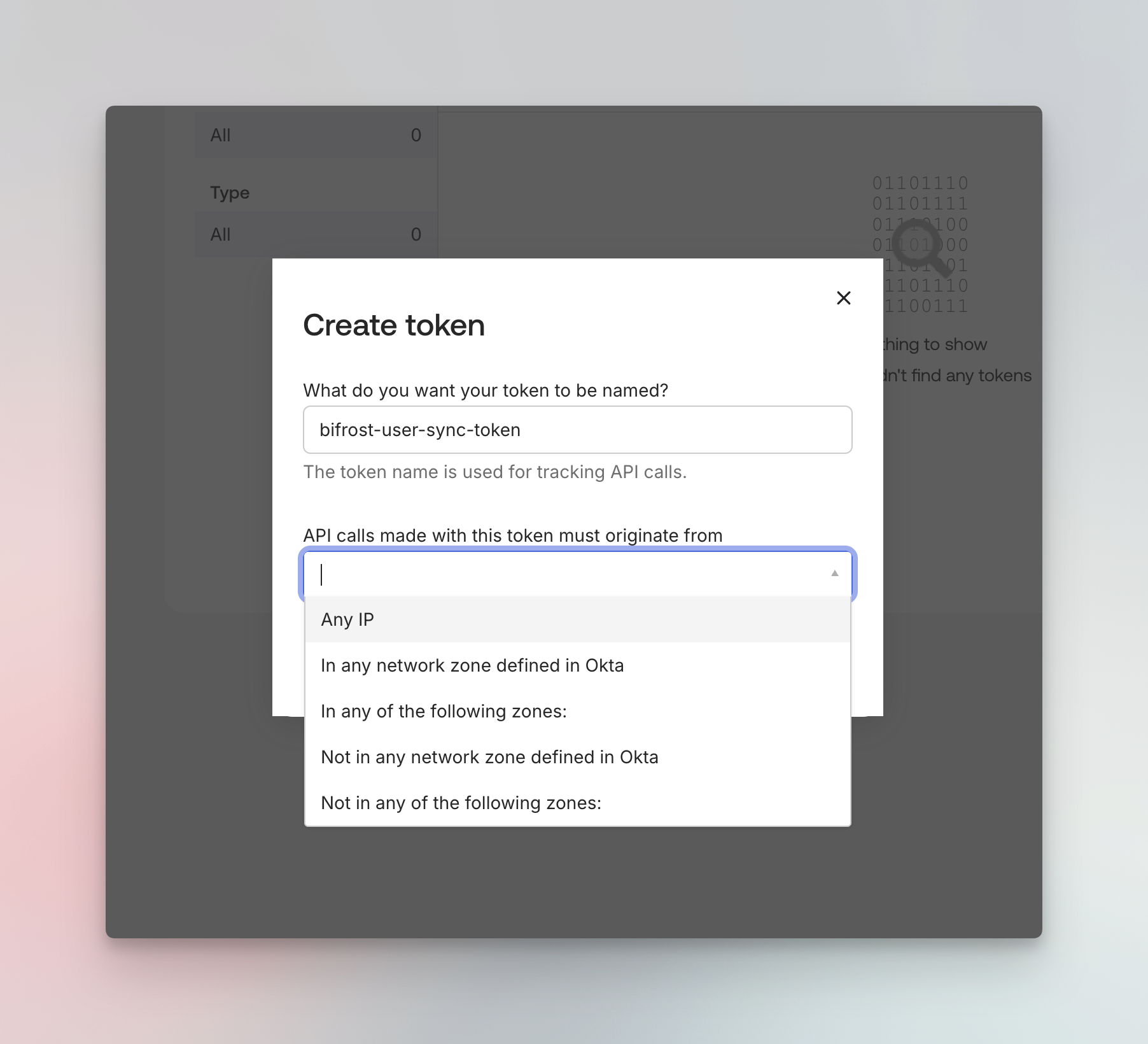
- Copy token to be used in the next step.
Step 8: Configure Bifrost
Now configure Bifrost to use Okta as the identity provider.Using the Bifrost UI
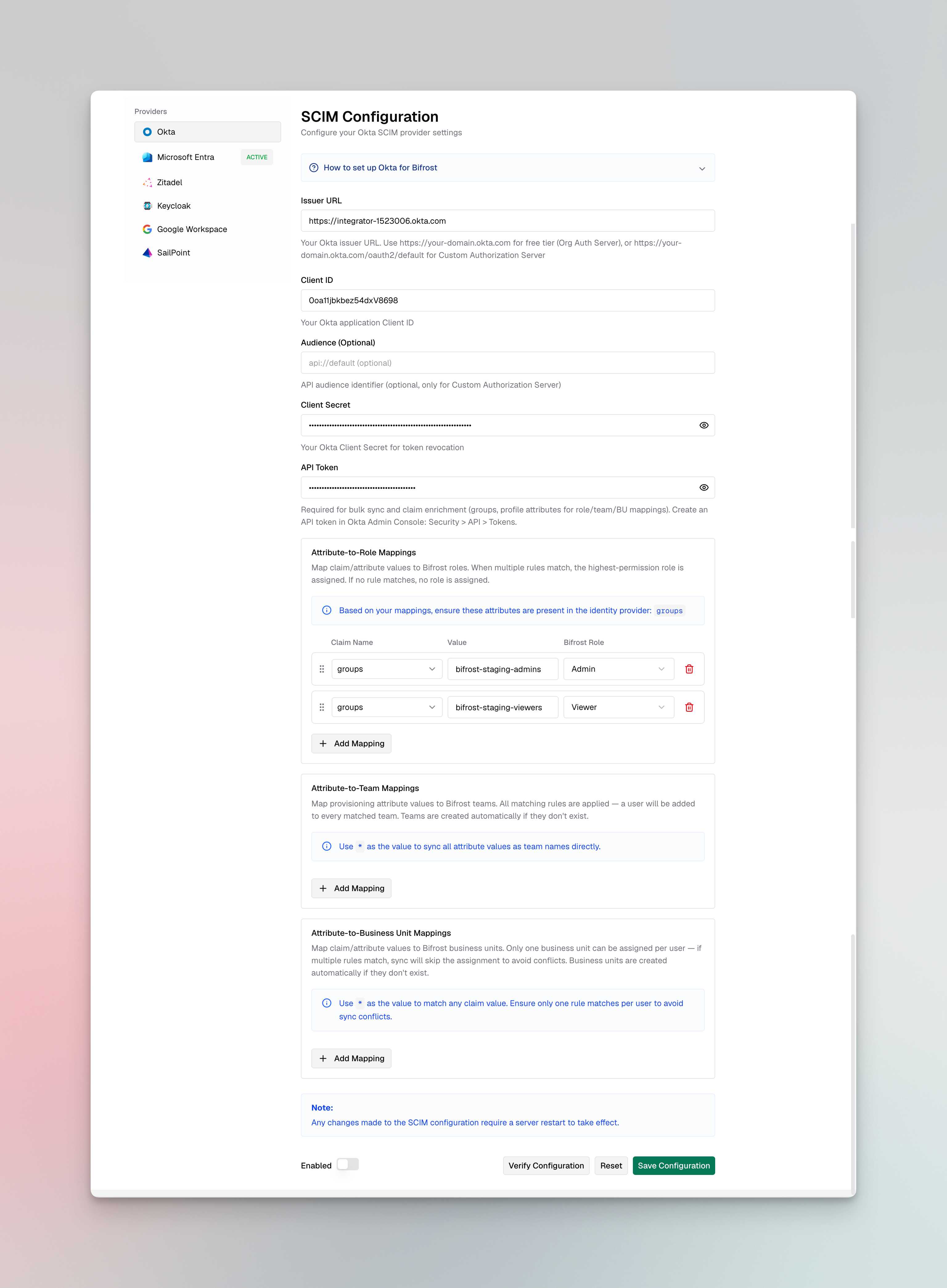
- Navigate to Governance → User Provisioning in your Bifrost dashboard
- Select Okta as the SCIM Provider
- Enter the following configuration:
| Field | Value |
|---|---|
| Client ID | Your Okta application Client ID |
| Issuer URL | Issuer URL |
| Audience | Your API audience (e.g., api://default or custom) |
| Client Secret | Your Okta application Client Secret (optional, for token revocation) |
- Verify configuration and see if you get any errors. Make sure you get no errors/warnings.
- Toggle Enabled to activate the provider
- Click Save Configuration
Attribute Mappings
Attribute mappings let you translate Okta claim values into Bifrost roles, teams, or business units without restructuring your Okta claims. Bifrost supports three mapping types:attributeRoleMappings: map a claim value to a Bifrost role (Admin, Developer, Viewer, or a custom role)attributeTeamMappings: map a claim value to a Bifrost teamattributeBusinessUnitMappings: map a claim value to a Bifrost business unit
groups claim from Step 5, the custom role claim from Step 4, or any other claim your authorization server includes in the token (e.g., department, organization).
To configure attribute mappings:
- In the User Provisioning configuration, scroll down to Attribute Mappings
- Click Add Mapping under the relevant mapping type (Role, Team, or Business Unit)
- Enter the Attribute (the claim name from the token), the Value to match, and the target Role, Team, or Business Unit
- Repeat for each rule you need
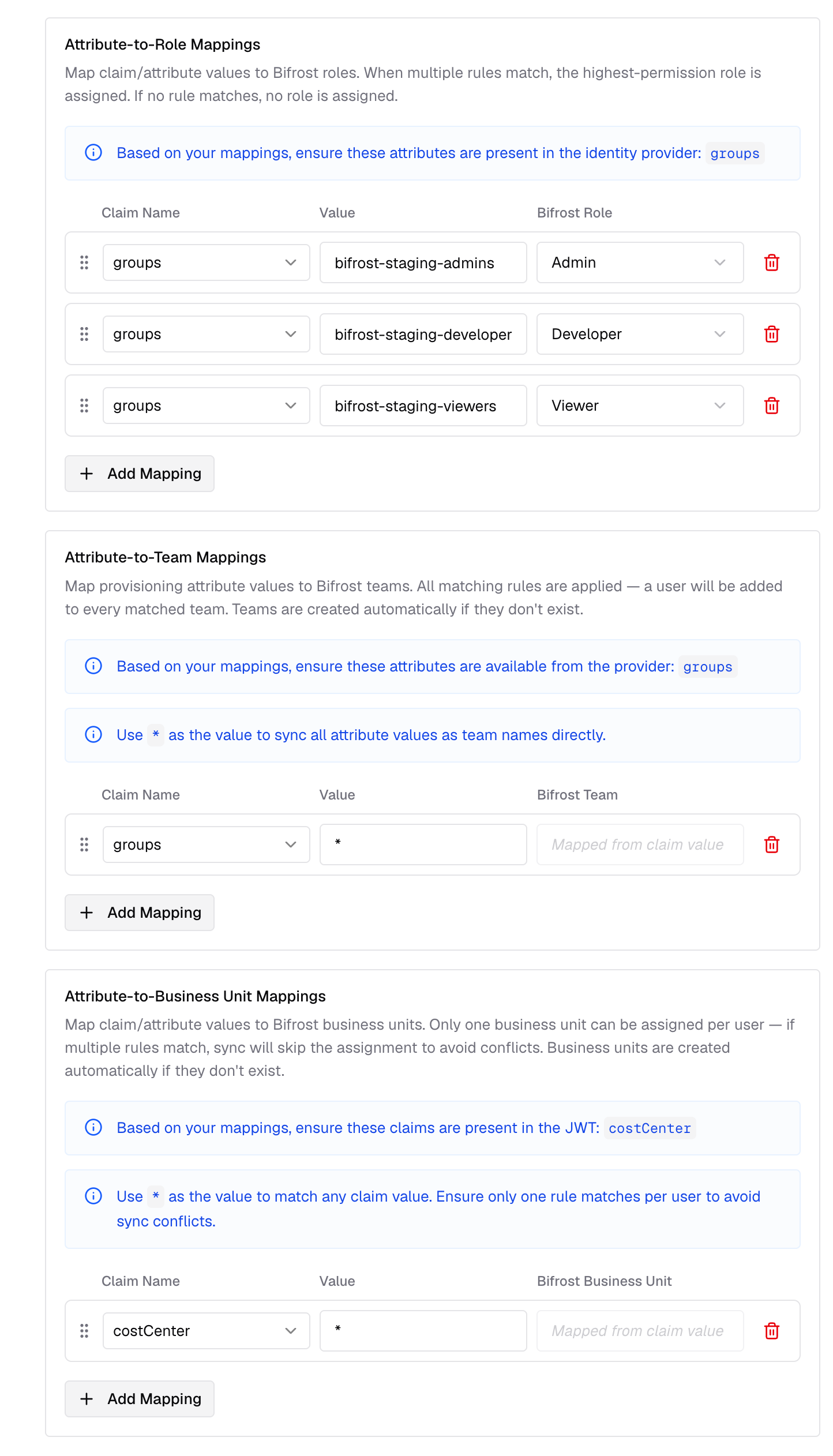
When you mark value as ”*” - the claim value is mapped as is to the entity name. Values comparisons are case-insensitive.
Custom attribute mapping
You can also map any custom attributes to any entity (role, team or business unit). Make sure these are configured to send back to Bifrost in token configuration.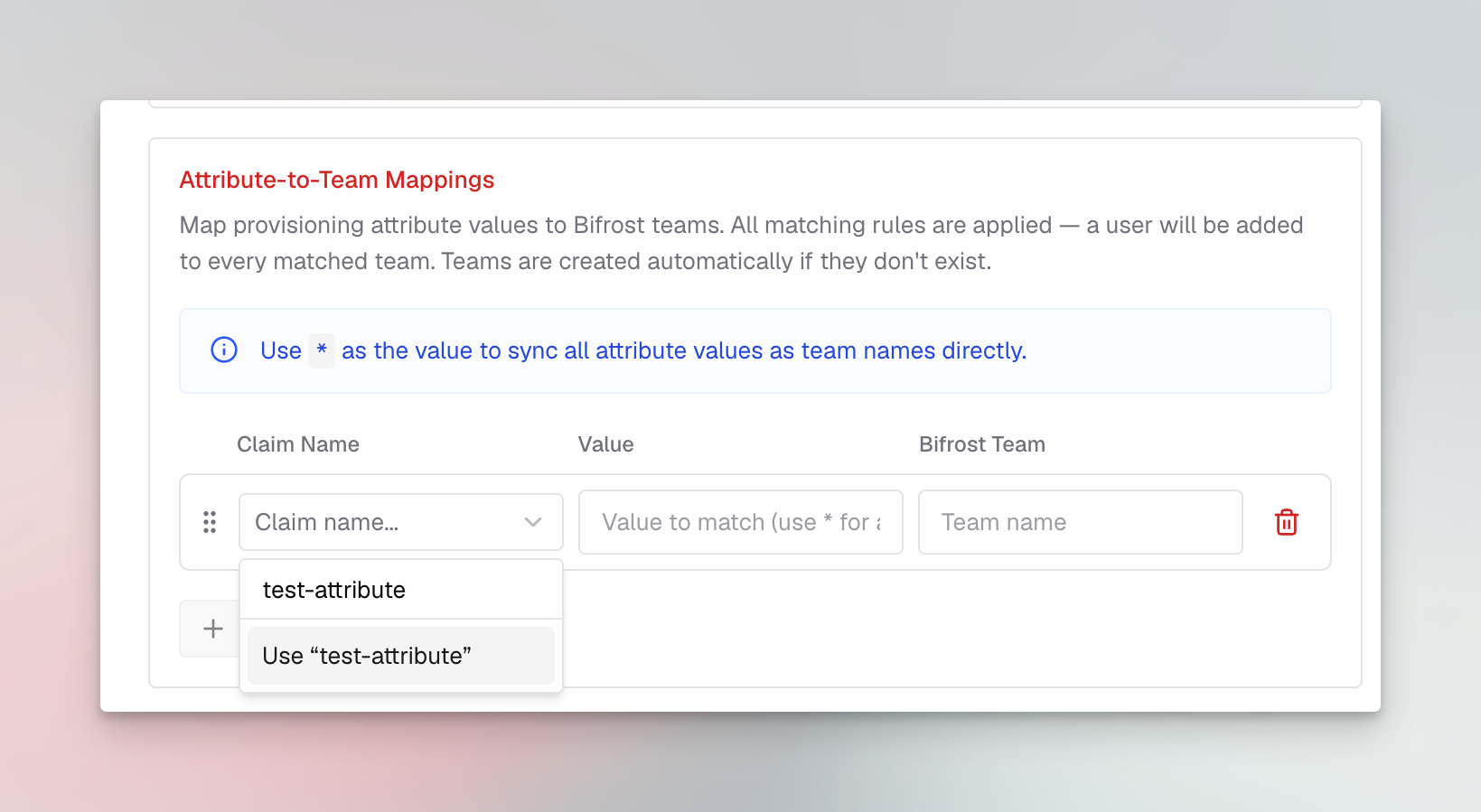
Evaluation rules
- Role mappings: Ordered, first match wins. If no rule matches, users are not allowed to login into the system.
- Team and business unit mappings: All matching rules apply - users can be placed on multiple teams and business units simultaneously.
- Claim values: Can be strings, arrays, or nested objects. Bifrost resolves dotted paths (e.g.,
realm_access.roles).
- Click Save Configuration
Configuration Reference
| Field | Required | Description |
|---|---|---|
issuerUrl | Yes | Okta authorization server URL (e.g., https://your-domain.okta.com/oauth2/default) |
clientId | Yes | Application Client ID from Okta |
clientSecret | Yes | Application Client Secret (enables token revocation) |
audience | Yes | API audience identifier from your authorization server |
attributeRoleMappings | Yes | Ordered list of attribute→role mappings. First match wins. |
attributeTeamMappings | No | Attribute→team mappings (all matches apply). |
attributeBusinessUnitMappings | No | Attribute→business-unit mappings (all matches apply). |
Testing the Integration
- Open your Bifrost dashboard in a new browser or incognito window
- You should be redirected to Okta for authentication
- Log in with an assigned user
- After successful authentication, you’ll be redirected back to Bifrost
- Verify the user appears in the Bifrost users list with the correct role
Troubleshooting
User not redirected to Okta
- Verify the SCIM provider is enabled in Bifrost
- Check that the Bifrost server was restarted after configuration
- Ensure the Issuer URL is correct and accessible
Attribute mapping is not working
- Verify that token configuration includes all the attributes used for mapping.
Token refresh failing
- Ensure the Refresh Token grant type is enabled for your application
- Verify the
offline_accessscope is included in your authorization requests
Next Steps
- User Provisioning (SCIM) - Overview of SCIM in Bifrost and alternative identity providers
- Advanced Governance - Learn about user budgets and compliance features
- Role-Based Access Control - Understand the Admin, Developer, Viewer hierarchy
- Audit Logs - Monitor user authentication and activity

