Documentation Index
Fetch the complete documentation index at: https://docs.getbifrost.ai/llms.txt
Use this file to discover all available pages before exploring further.
Overview
This guide walks you through configuring Google Workspace as your identity provider for Bifrost Enterprise. The integration has two pieces:- OAuth 2.0 login - users sign in to Bifrost with their Google Workspace accounts via a Google OAuth Client ID.
- Directory API provisioning (optional) - a Google service account with domain-wide delegation lets Bifrost list users and groups from the Workspace directory for bulk import and team sync.
Prerequisites
- A Google Workspace domain with Super Admin access to the Admin console
- A Google Cloud project where you can create OAuth clients and service accounts
- Bifrost Enterprise deployed and accessible
- The redirect URI for your Bifrost instance (e.g.
https://your-bifrost-domain.com/login) - Bifrost roles created for the roles you plan to map
Step 1: Configure the OAuth consent screen
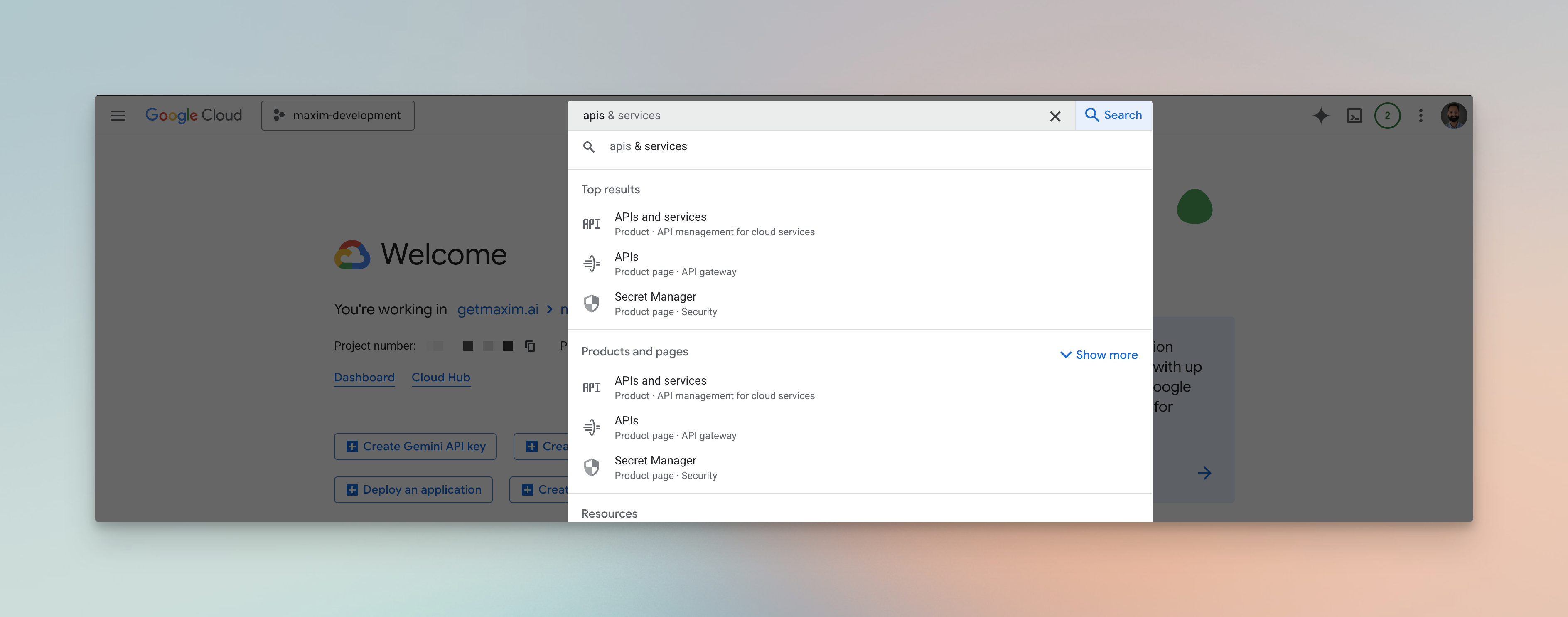
- In the Google Cloud Console, go to APIs & Services → OAuth consent screen.
- Choose Internal if you only want Workspace users, or External otherwise.
- Fill in App name, support email, and developer contact.
- Add the scopes:
openid,profile,email. - Save.
Step 2: Create an OAuth Client ID
- Open APIs & Services → Credentials → Create credentials → OAuth client ID.
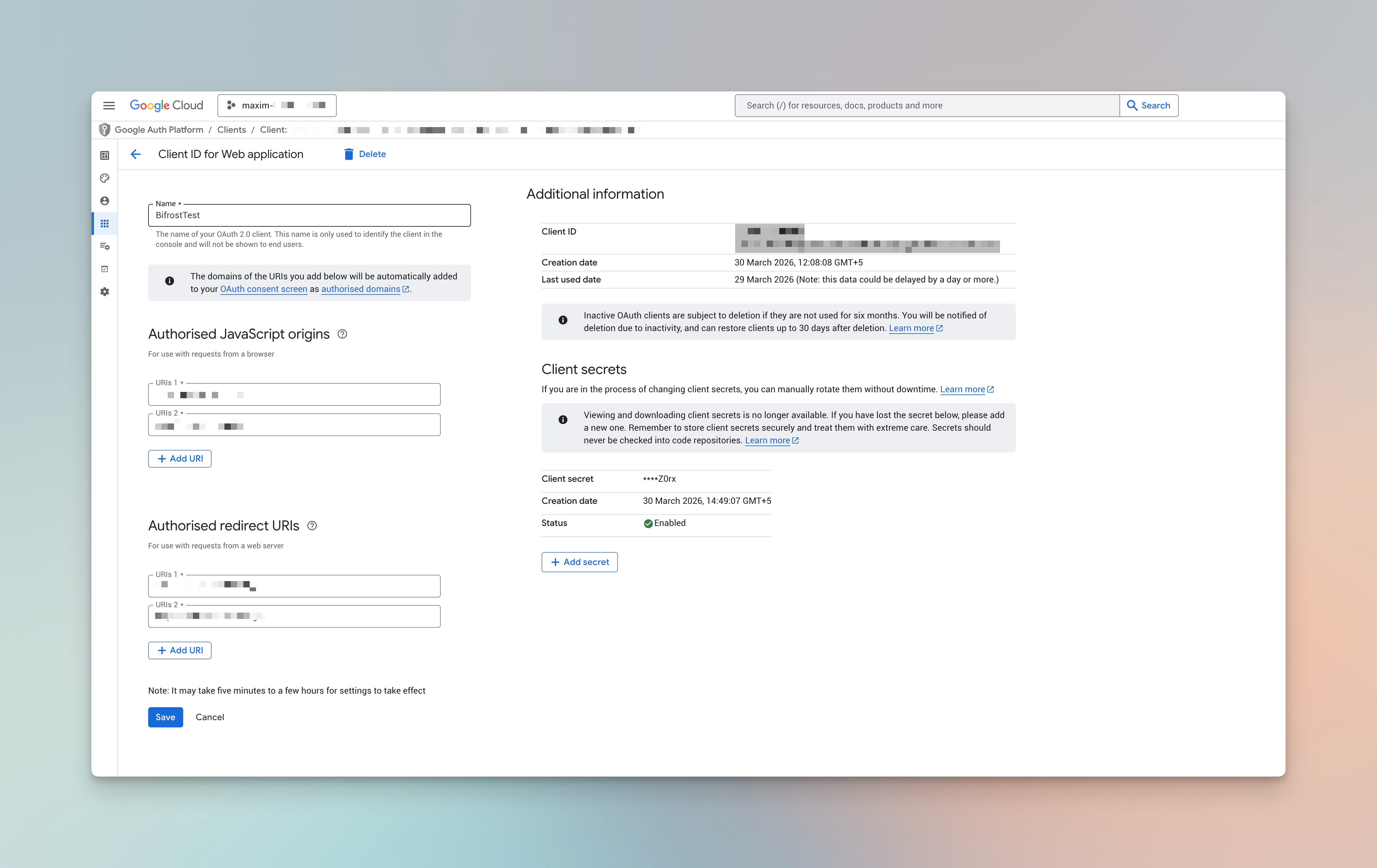
- Configure:
| Field | Value |
|---|---|
| Application type | Web application |
| Name | Bifrost Enterprise |
| Authorized JavaScript origins | https://your-bifrost-domain.com |
| Authorized redirect URIs | https://your-bifrost-domain.com/login |
- Save and copy the Client ID and Client Secret.
Step 3: (Optional) Create a service account for Directory API access
Skip this section if you only want SSO login without directory-based user import.- Go to IAM & Admin → Service Accounts → Create service account.
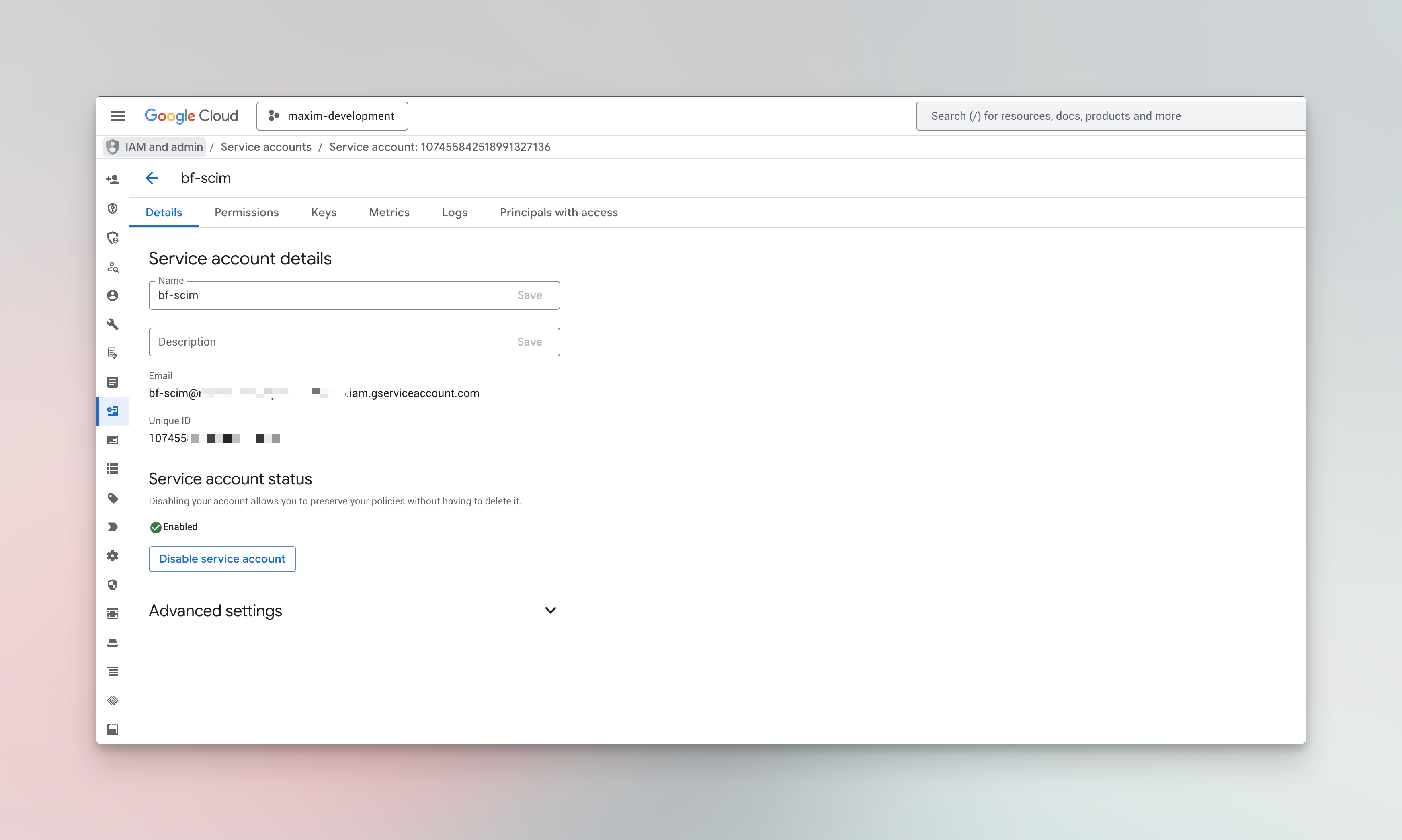
- Give it a name (e.g.
bifrost-provisioning). You can skip the “Grant this service account access to project” step - no GCP IAM roles are required; access is granted via domain-wide delegation in Step 5. - Open the service account → Keys → Add Key → Create new key → JSON. Download and store the JSON file securely.
- From the service account Details tab, copy the Unique ID (a numeric value, not the email or OAuth Client ID).
Step 4: Enable the Admin SDK API
If you’re using the service account path:- Open APIs & Services → Library.
- Search for Admin SDK API and click Enable.
Step 5: Set up domain-wide delegation
- In the Google Admin Console, go to Security → Access and data control → API controls → Manage Domain Wide Delegation.
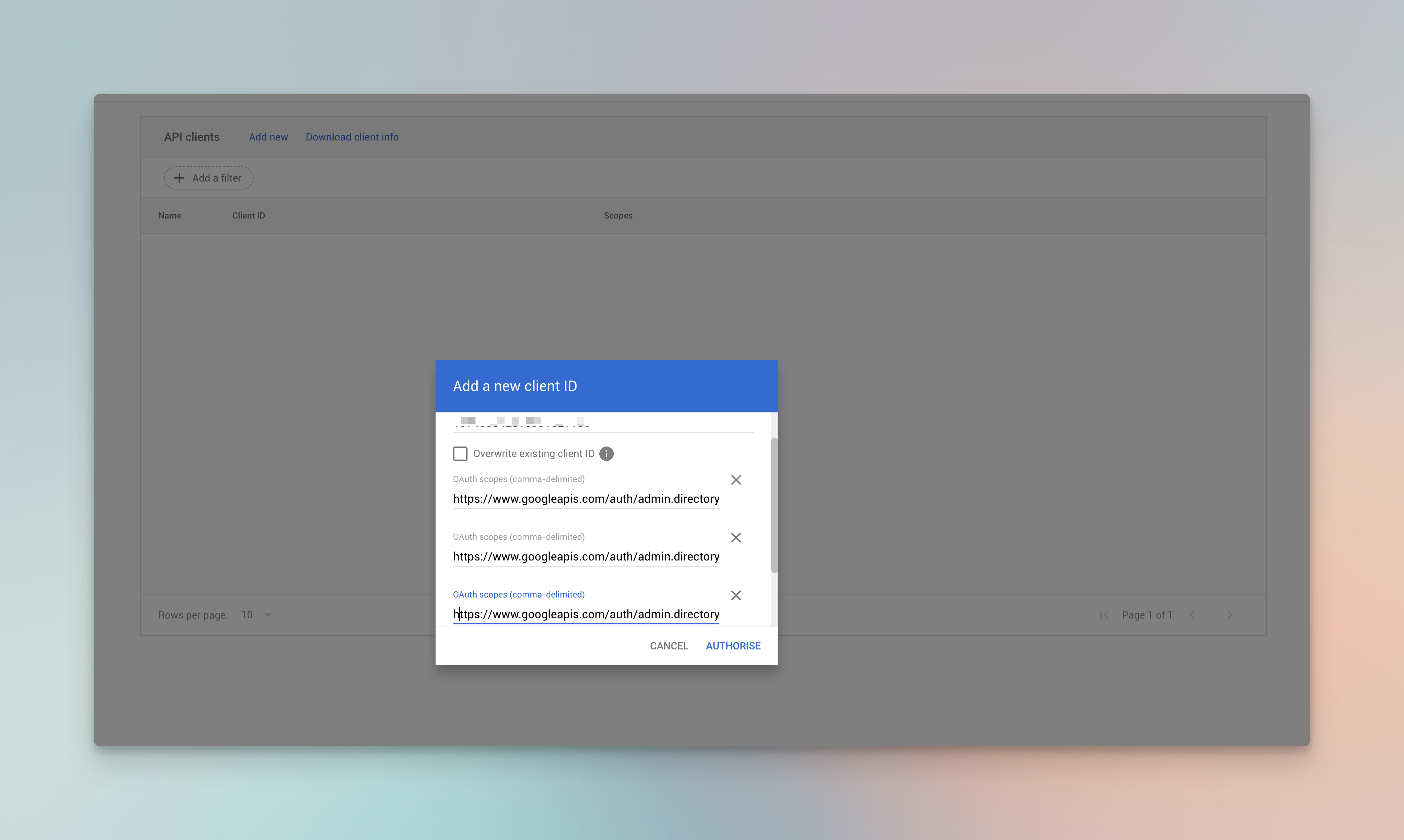
- Click Add new.
- Enter the service account’s Unique ID (from Step 3).
- Add these OAuth scopes (copy the full URLs, comma-separated):
- Authorize.
Domain-wide delegation requires impersonating an admin user. Pick an admin email that will persist (e.g. a dedicated
[email protected]) - Bifrost uses this as the Admin Email in configuration.Step 6: Configure Bifrost
Using the Bifrost dashboard
- In Bifrost, go to Governance → User Provisioning.
- Select Google Workspace as the OIDC Provider.
- Fill in the fields:
| Field | Value |
|---|---|
| Domain | Your Google Workspace primary domain (e.g. company.com) |
| Client ID | OAuth Client ID from Step 2 |
| Client Secret | OAuth Client Secret from Step 2 |
| Audience | Optional override (defaults to Client ID) |
| Admin Email | Admin user to impersonate for Directory API (Step 5) |
| Service Account Source | Choose one: Paste JSON / Environment variable / File path |
| Service Account JSON / Env Var / File | The value for the chosen source |

- Click Verify - Bifrost validates the OAuth client and, if a service account is provided, attempts a Directory API impersonation to confirm delegation is working.
- Configure Attribute → Role / Team / Business Unit mappings to map groups or organizational units to Bifrost roles and teams.
- Toggle Enabled and click Save Configuration.
Using config.json
serviceAccountJson (raw JSON string), serviceAccountEnvVar (env var name holding the JSON), or serviceAccountFile (absolute path to the key file).
Custom attribute mapping
You can also map any custom attributes to any entity (role, team or business unit). Make sure these are configured to send back to Bifrost in token configuration.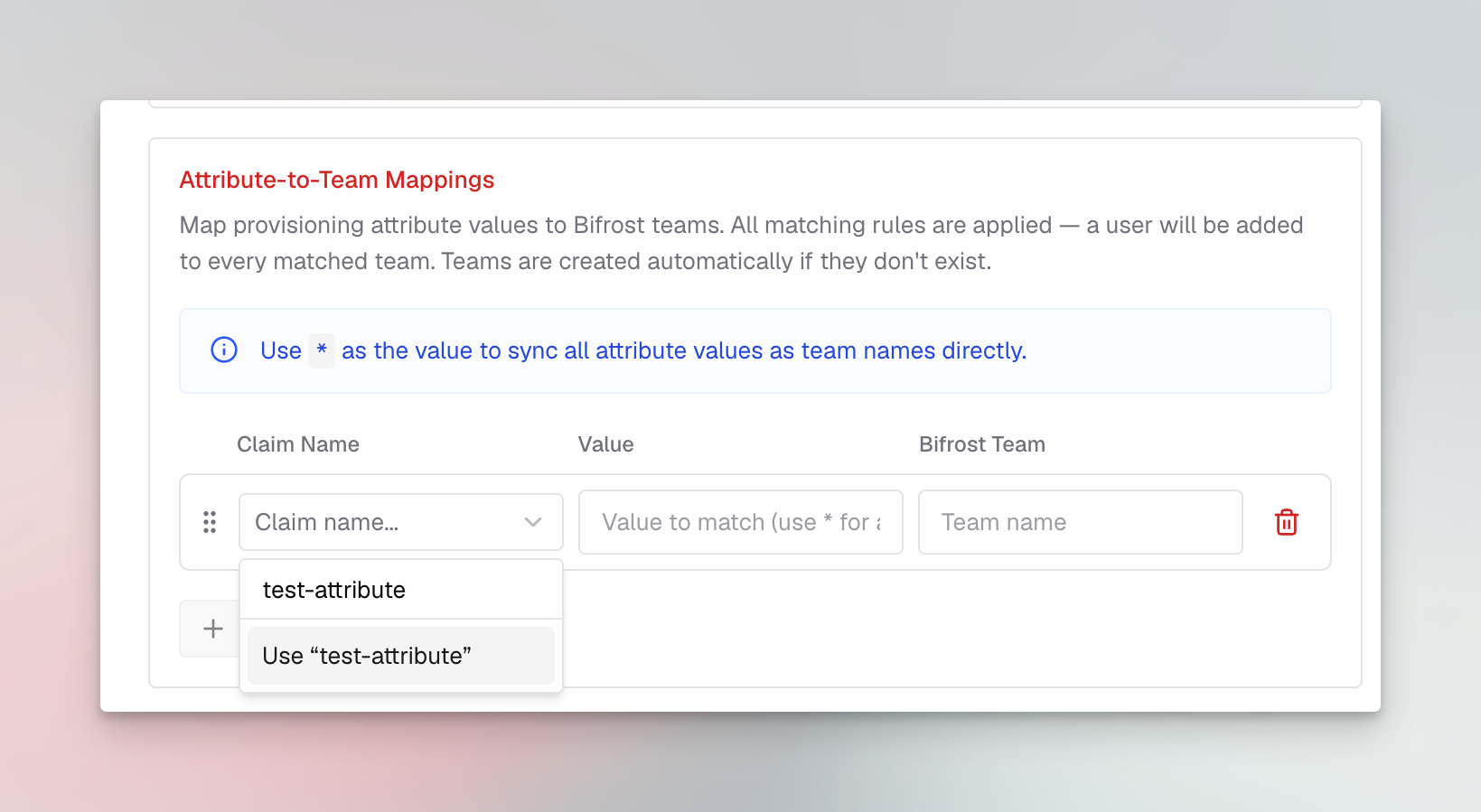
Configuration reference
| Field | Required | Description |
|---|---|---|
domain | Yes | Google Workspace primary domain (e.g. company.com). |
clientId | Yes | OAuth 2.0 Web Client ID from Step 2. |
clientSecret | Yes | Client Secret - required for token revocation and for confidential server-side flows. |
audience | No | Expected JWT audience. Defaults to clientId. |
adminEmail | Yes | Workspace admin to impersonate via domain-wide delegation. Required when any service-account field is set. |
serviceAccountJson | One of 3 | Raw JSON string of the service account key. |
serviceAccountEnvVar | One of 3 | Name of the environment variable containing the JSON. |
serviceAccountFile | One of 3 | Absolute path to the JSON key file on the Bifrost host. |
attributeRoleMappings | Yes | Ordered list of attribute→role mappings. |
attributeTeamMappings | No | Attribute→team mappings (all matches apply). |
attributeBusinessUnitMappings | No | Attribute→business-unit mappings (all matches apply). |
Background user sync
Bifrost does not currently support Google Workspace SCIM management APIs or inbound Google Workspace SCIM provisioning. Do not configure an external SCIM provisioning app for Bifrost yet. For Google Workspace, Bifrost uses the Directory API setup above to sync users in the background every 24 hours. During that sync, Bifrost reconciles imported users, role mappings, team mappings, and business-unit mappings from Google Workspace. Every 15 minutes, Bifrost also refreshes active OIDC sessions. If a session cannot be refreshed, Bifrost checks with Google whether the user is still active; if Google reports the user is inactive, Bifrost decommissions that user locally. Support for Google Workspace SCIM management APIs is coming soon.Testing the Integration
- Open the Bifrost dashboard in an incognito window.
- You’re redirected to
accounts.google.com; sign in with a Workspace user. - Verify you land on the Bifrost dashboard and appear under Governance → Users.
- If provisioning is configured, open Governance → User Provisioning → Import Users, filter by a Workspace group, click Preview, and confirm users show up.
Troubleshooting
admin_policy_enforced or access_denied during OAuth
- The Workspace admin has blocked third-party OAuth apps. In the Admin Console, go to Security → Access and data control → API controls and allow the Bifrost OAuth client.
unauthorized_client: Client is unauthorized to retrieve access tokens
- The service account Unique ID and scopes in Domain-Wide Delegation don’t match. Re-enter the Unique ID (the numeric value from the service account’s Details tab, not the OAuth client ID).
Not Authorized to access this resource/api from Directory API
- The impersonated
adminEmailis missing the User Management Admin role. Promote them in Admin Console → Admin roles. - The Admin SDK API is not enabled on the Cloud project.
Users see a consent prompt every login
- On the OAuth consent screen, ensure the app is Published (or Internal for Workspace-only apps) so it doesn’t stay in testing mode.
domain_mismatch
- The primary domain in the Workspace does not match the
domainfield. Use the primary domain, not an alias.
Next Steps
- User Provisioning overview - capabilities, attribute mappings, bulk import
- Role-Based Access Control - configure custom roles before mapping
- Audit Logs - track authentication events

