Documentation Index
Fetch the complete documentation index at: https://docs.getbifrost.ai/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Per-user OAuth is available in Bifrost v1.5.0-prerelease2 and above.
| Server-level OAuth | Per-user OAuth | |
|---|---|---|
| Who authenticates | Admin, once | Each end-user individually |
| Token scope | Shared across all requests | Per-user, per-service |
| Identity required | No | Yes (VK, User ID, or session) |
| Persists across sessions | Yes (background refresh) | Yes, when tied to VK or User ID |
| Works with MCP Gateway | Yes | Yes |
| Works with LLM Gateway | Yes | Yes |
Setup
Per-user OAuth is configured through the Web UI only. During setup, Bifrost runs a test OAuth flow and pre-fetches the available tools from the upstream service - this is why file-based config is not supported for this auth type.- Web UI
- Navigate to MCP Gateway and click New MCP Server
- Select HTTP or SSE as the connection type and enter the server URL
- Set Auth Type to Per-User OAuth
-
Fill in the OAuth application credentials:
- Client ID - your upstream OAuth app’s client ID
- Client Secret - optional for PKCE flows
- Authorize URL - upstream authorization endpoint (or leave blank for auto-discovery)
- Token URL - upstream token endpoint (or leave blank for auto-discovery)
- Scopes - comma-separated list of requested scopes
- Click Create - Bifrost runs a test OAuth flow to validate the config and pre-fetches the tool list
- Complete the authorization in your browser
-
Save the MCP client
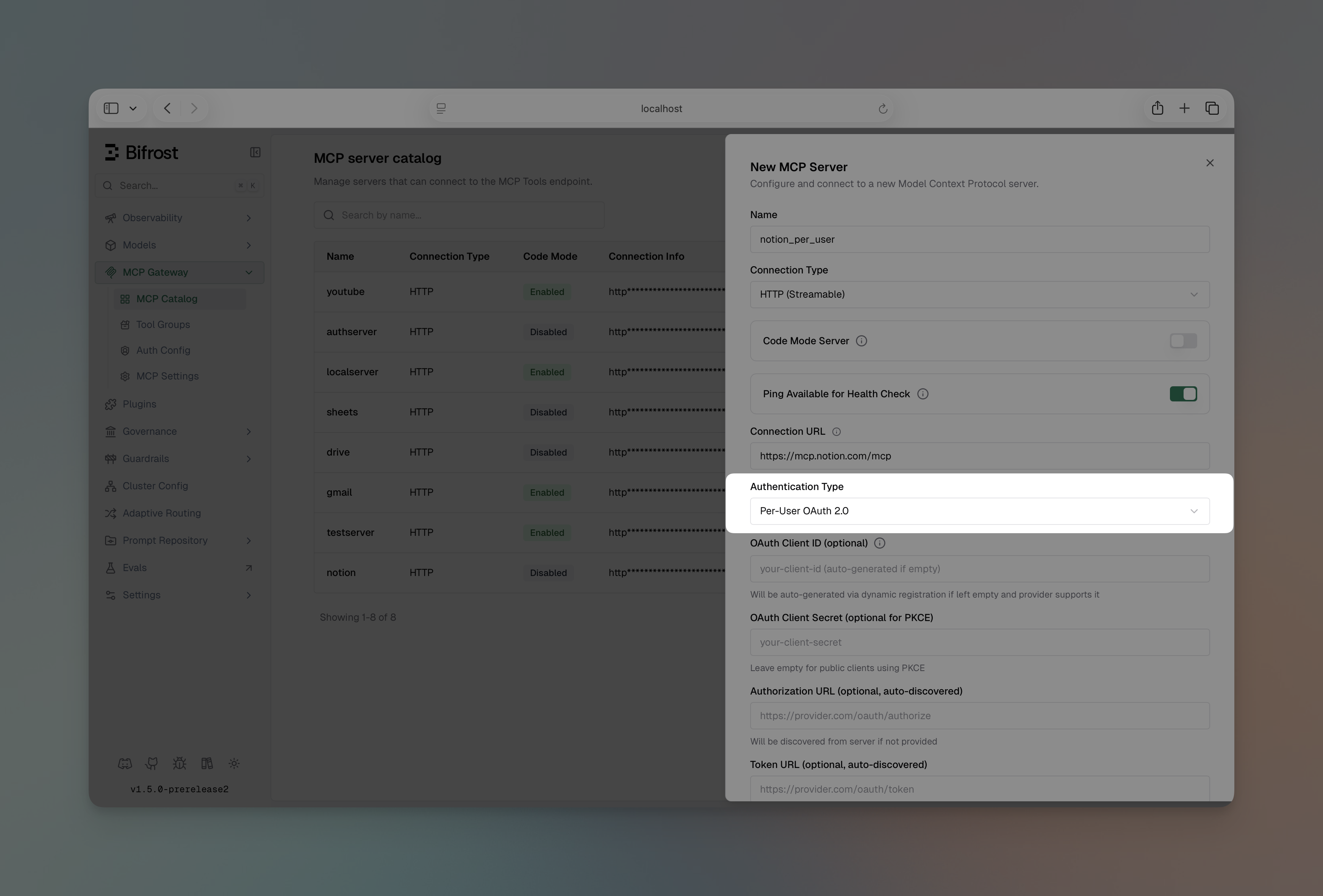
If your upstream server supports OAuth Discovery (RFC 8414), you can leave the authorize and token URLs blank and provide only the Server URL. Bifrost will discover the endpoints automatically.
How it works: MCP Gateway
When you expose Bifrost as an MCP server (via the/mcp endpoint) and at least one MCP client is configured with per_user_oauth, Bifrost becomes an OAuth 2.1 Authorization Server. OAuth-capable MCP clients like Claude Code and Cursor detect this automatically - no manual configuration required on the client side.
The full flow involves three distinct phases: discovery (the client finds Bifrost’s OAuth endpoints), consent (the user attaches an identity and connects upstream services), and authenticated use (all subsequent tool calls carry the user’s tokens transparently). The diagram below shows all three phases end to end.

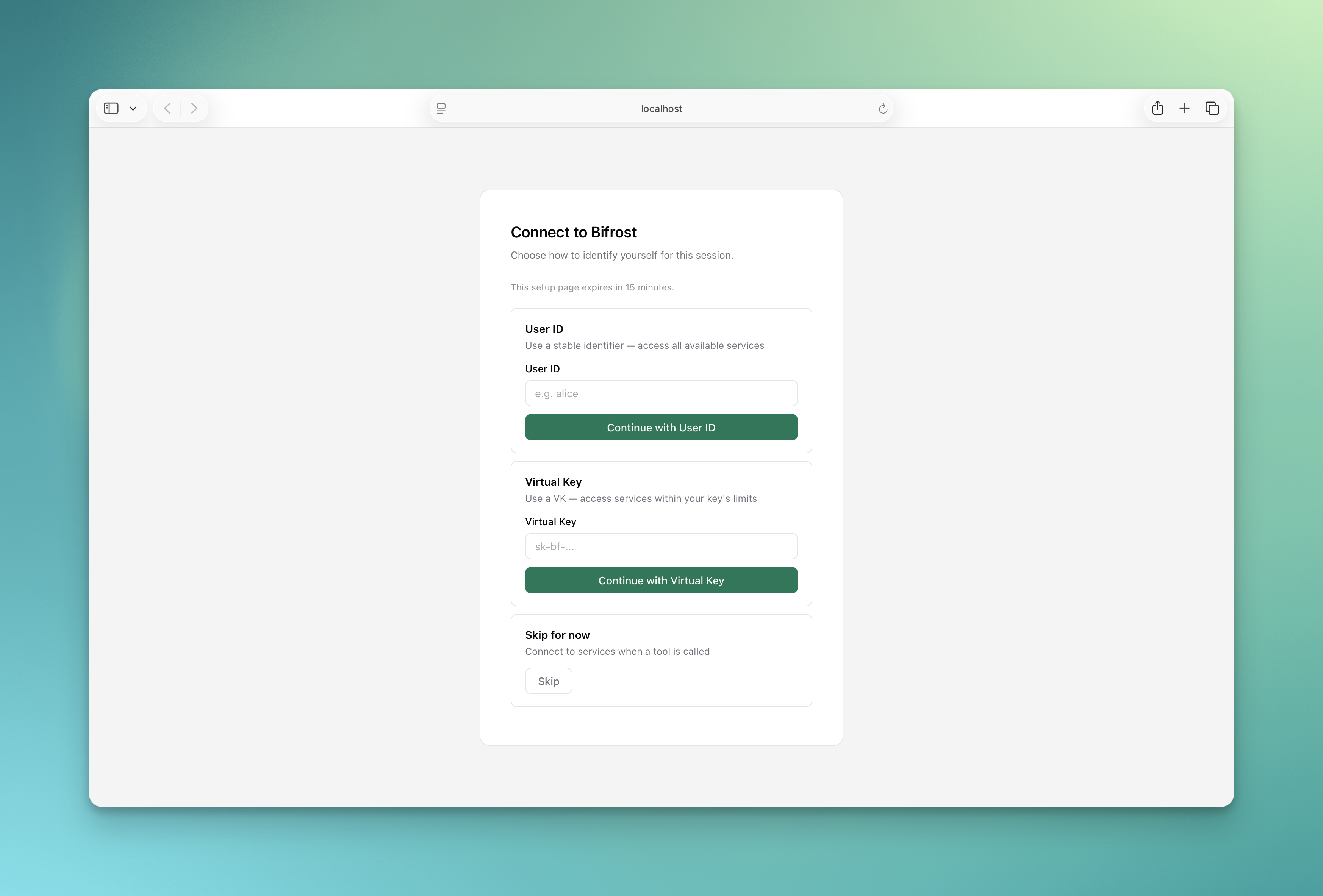
First connection: the consent flow
The first time a client connects, Bifrost walks the user through a two-step consent screen: Step 1 - Identity selection The user chooses how to identify themselves for this session:- Virtual Key - ties upstream tokens to the VK permanently; tokens survive session restarts and work across the LLM Gateway too
- User ID - a self-declared identifier with the same persistence guarantees as a VK
- Skip - no identity attached; tokens are scoped to this session only and won’t carry over to other sessions or the LLM Gateway
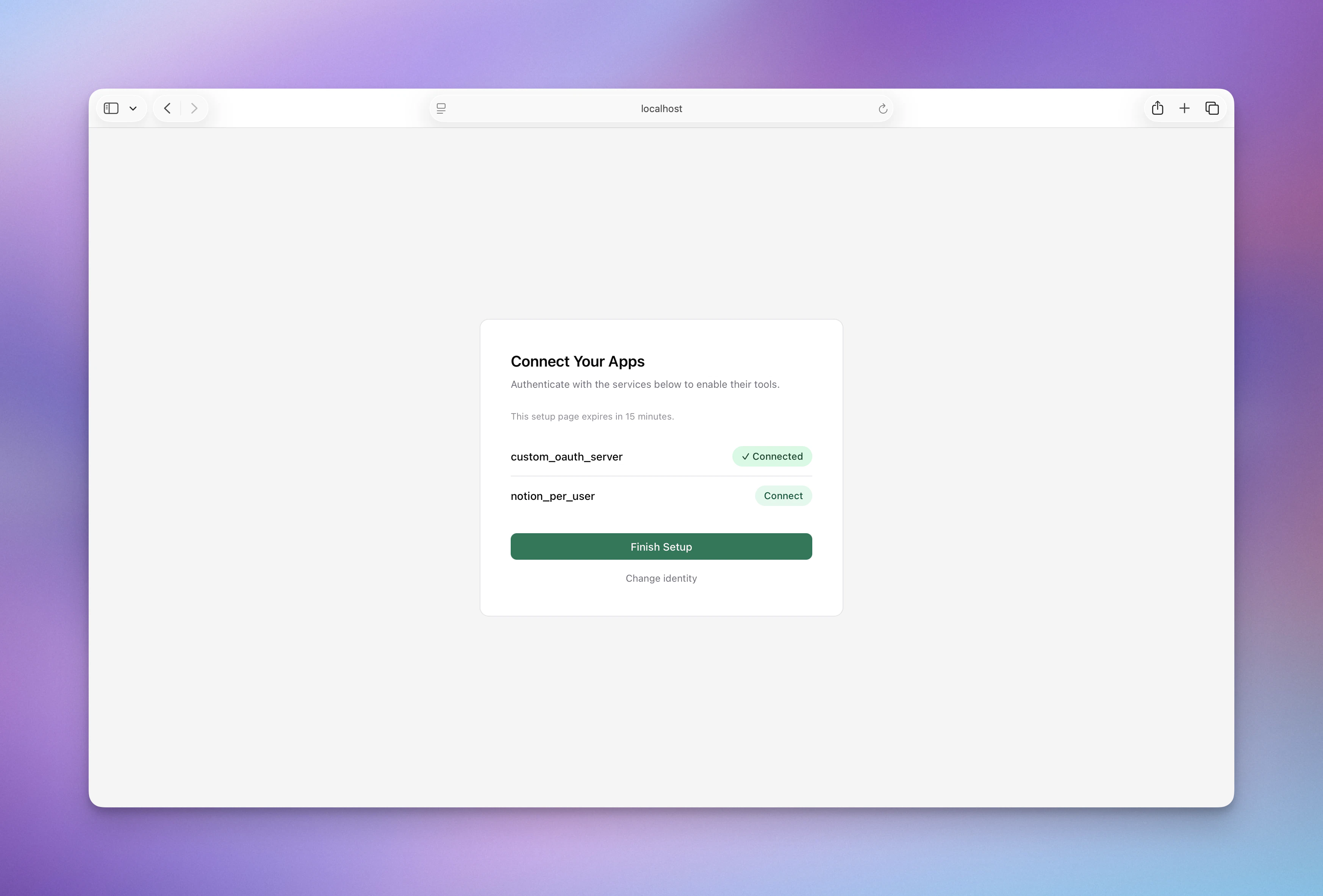
Lazy auth for skipped services
If the user skips a service during consent - or a new per-user MCP server is added later - Bifrost handles it lazily. When a tool call hits a service the user hasn’t authenticated with yet, Bifrost returns an auth URL in the tool result instead of executing the tool: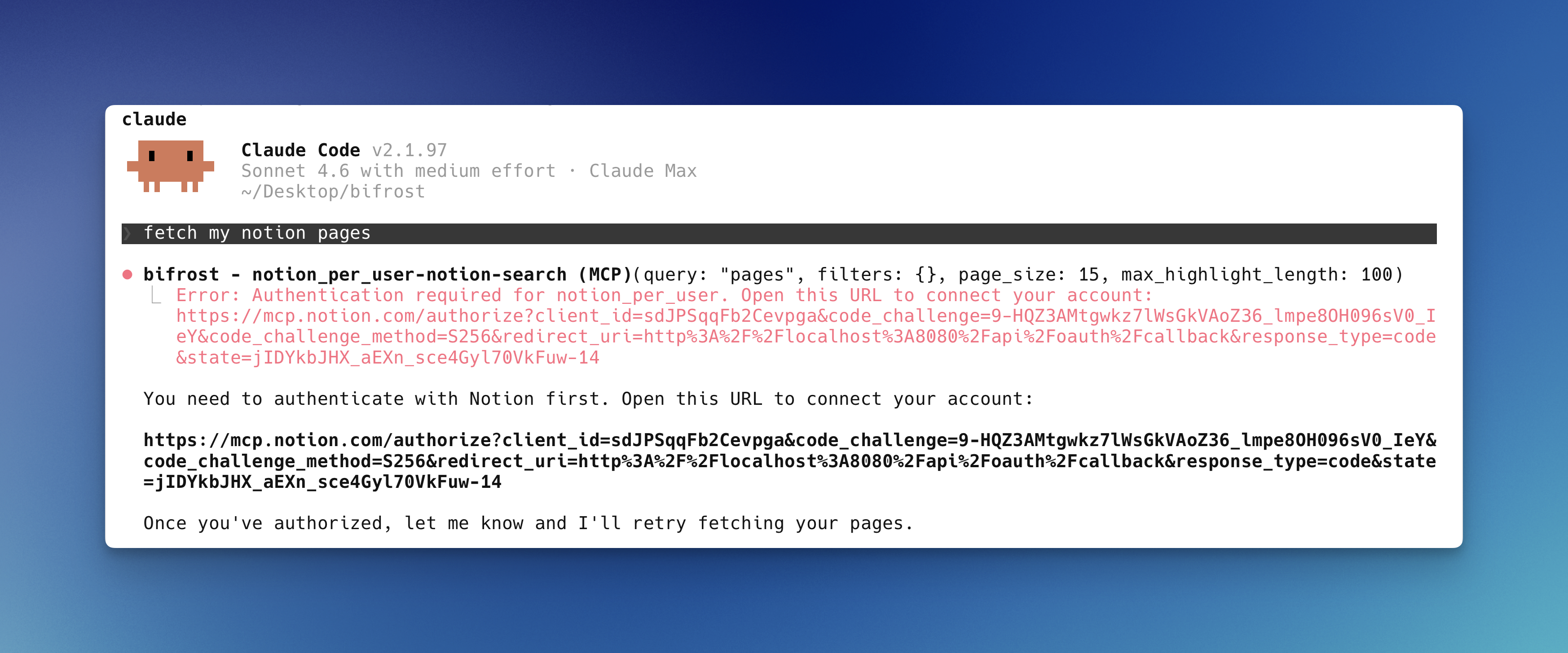
How it works: LLM Gateway
When using per-user OAuth through the LLM Gateway (/v1/chat/completions), there is no upfront consent screen. Auth is entirely lazy - Bifrost waits until a tool actually needs a token before asking for one. This is also the same pattern used when a service is skipped during MCP Gateway consent.
The pattern is simple: every request carries an identity header, and any tool call to an unauthenticated service returns an auth URL instead of a result. The user completes auth once at that URL; all subsequent calls to that service execute normally. The diagram below shows the full cycle.

- The user makes a request with an identity header attached (required - see below)
- The LLM suggests a tool call to a per-user OAuth service
- If no token exists for that user + service, Bifrost returns an
mcp_auth_requiredresponse with anauthorize_urlinstead of executing the tool - the rest of the LLM response still comes through normally
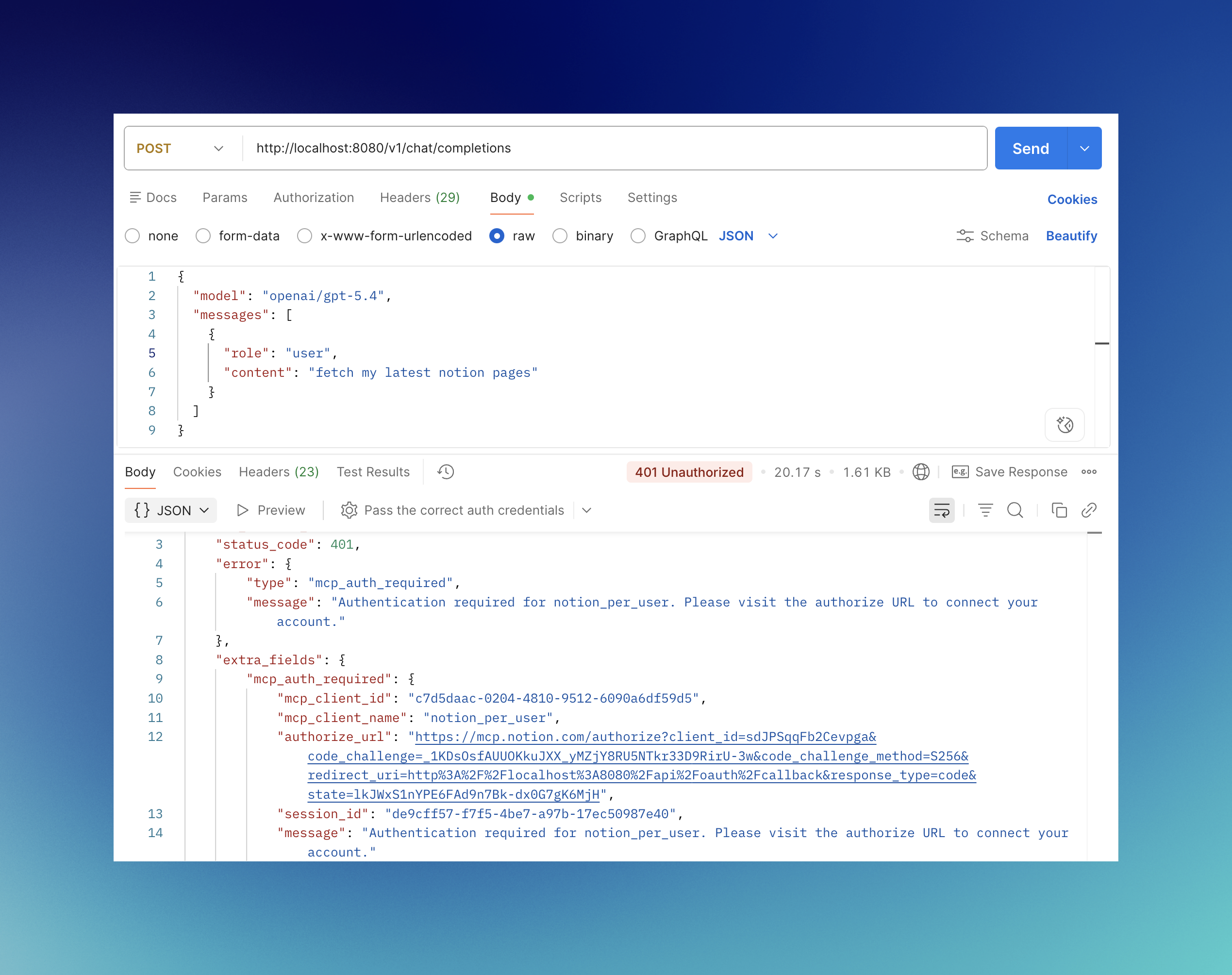
- The user opens the URL and completes the upstream OAuth flow
- Bifrost saves the token against their identity - no action needed on your side
- On the next request, the tool call executes normally - no re-auth, no special handling required
Identity is required
The LLM Gateway has no session management, so an identity must be declared on every request. Without one, Bifrost has no stable key to look up or store tokens against. Pass one of:Enterprise: When enterprise user identity is configured, the user’s identity is automatically attached as the User ID - no manual header required.
Cross-gateway token sharing
Tokens are stored against an identity (Virtual Key or User ID), not against a gateway. This means:- Authenticate via the LLM Gateway with a VK → that token is immediately usable on the MCP Gateway with the same VK
- Authenticate via the MCP Gateway consent flow with a VK → that VK works on the LLM Gateway with no re-auth needed
| Identity mode | Set via | Cross-gateway portable | Persists across sessions |
|---|---|---|---|
| Virtual Key | Consent screen or x-bf-virtual-key header | Yes | Yes |
| User ID | Consent screen or X-Bf-User-Id header | Yes | Yes |
| Skip (MCP Gateway only) | Consent screen | No | No |
Config reference
Per-user OAuth is configured on the MCP client viaauth_type. When auth_type is per_user_oauth, an oauth_config_id linking to the OAuth credentials is required (set automatically during UI setup):
| Field | Type | Description |
|---|---|---|
auth_type | string | Set to "per_user_oauth" |
oauth_config_id | string | ID of the OAuth config created during UI setup |
Next Steps
- Server-level OAuth → - admin authenticates once, shared token for all requests
- MCP Gateway URL → - expose Bifrost as an MCP server for Claude Code and Cursor
- Tool Filtering → - control which per-user tools are available per Virtual Key

