Bifrost applies defense-in-depth across its open-source and enterprise repositories. Every pull request, dependency update, and container image goes through multiple layers of automated security checks before reaching production.Documentation Index
Fetch the complete documentation index at: https://docs.getbifrost.ai/llms.txt
Use this file to discover all available pages before exploring further.
| Domain | Tool / Practice | Coverage |
|---|---|---|
| Dependency Scanning | Snyk Open Source | Go, Node, Python - all projects |
| SAST | Snyk Code, CodeQL | Full codebase static analysis |
| Container Scanning | Docker Scout | Docker Hub auto-scan on push |
| Artifact Scanning | GCP Artifact Registry | Enterprise container images |
| Dependency Updates | Dependabot | gomod, npm, Docker, GitHub Actions |
| Supply Chain | SHA pinning, npm provenance | 100 % of GitHub Actions (OSS) |
| Container Hardening | FIPS base image, non-root user | Production Dockerfile |
| Security Hardening | StepSecurity, CODEOWNERS | Workflow hardening, code review gates |
| Network Security | Tailscale VPN | Enterprise deployments |
Vulnerability Scanning - Snyk
Bifrost runs two Snyk scanning jobs on every push and pull request. Results are uploaded as SARIF to the GitHub Security tab.- Dependency Scanning (Open Source)
- SAST (Snyk Code)
The Snyk Open Source job scans all Go, Node, and Python dependencies for known vulnerabilities.
- Scans every module across
core/,framework/,transports/,plugins/,ui/, andtests/ - Detection depth of 4 catches transitive dependencies
- Snyk CLI pinned to
v1.1303.2
Snyk checks can be skipped by including
--skip-ci in the first line of a commit message. This is
intended for documentation-only or CI configuration changes.Container Image Security
Dockerfile Hardening
Production containers follow a strict hardening checklist:Multi-stage builds
Three stages - UI builder (Node), Go builder, and minimal Alpine runtime - ensure no build tools or
source code leak into the final image.
FIPS-compliant base image
Production images use a FIPS 140-2 validated Alpine base image with compliant OpenSSL.
Non-root execution
The FIPS base image includes a dedicated
appuser. The container runs as this unprivileged user -
never as root.Binary stripping
Go binaries are compiled with
-ldflags="-w -s" to strip debug symbols and DWARF information,
reducing attack surface and image size.- Static builds - Compiled with
-tags "sqlite_static"and-extldflags '-static'for fully static linking - Build verification -
RUN test -f /app/main || exit 1ensures the binary exists before proceeding - CVE patching - Enterprise Dockerfiles include targeted patches (e.g.,
apk upgrade --no-cache opensslfor CVE-2026-22796) - Minimal runtime dependencies - The FIPS base image provides only essential libraries (
musl,libgcc,ca-certificates)
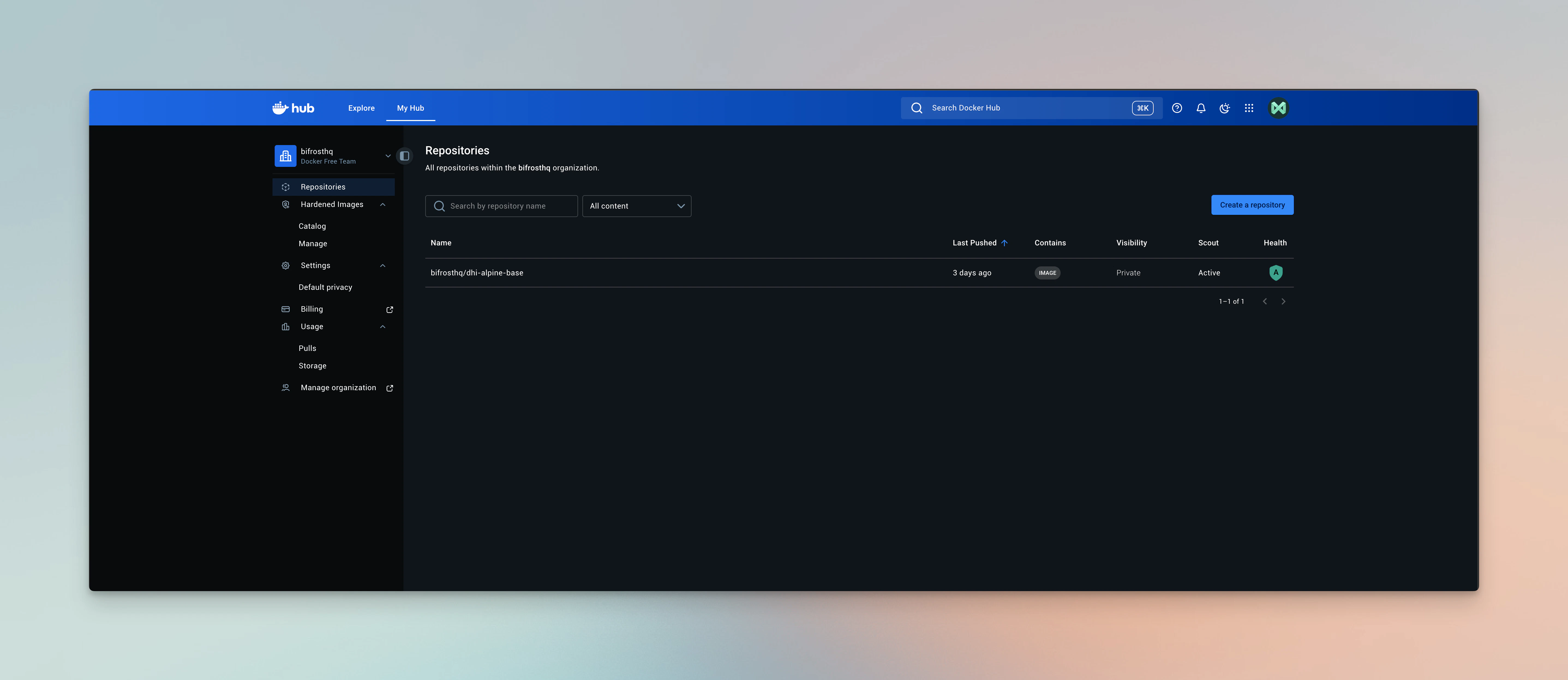
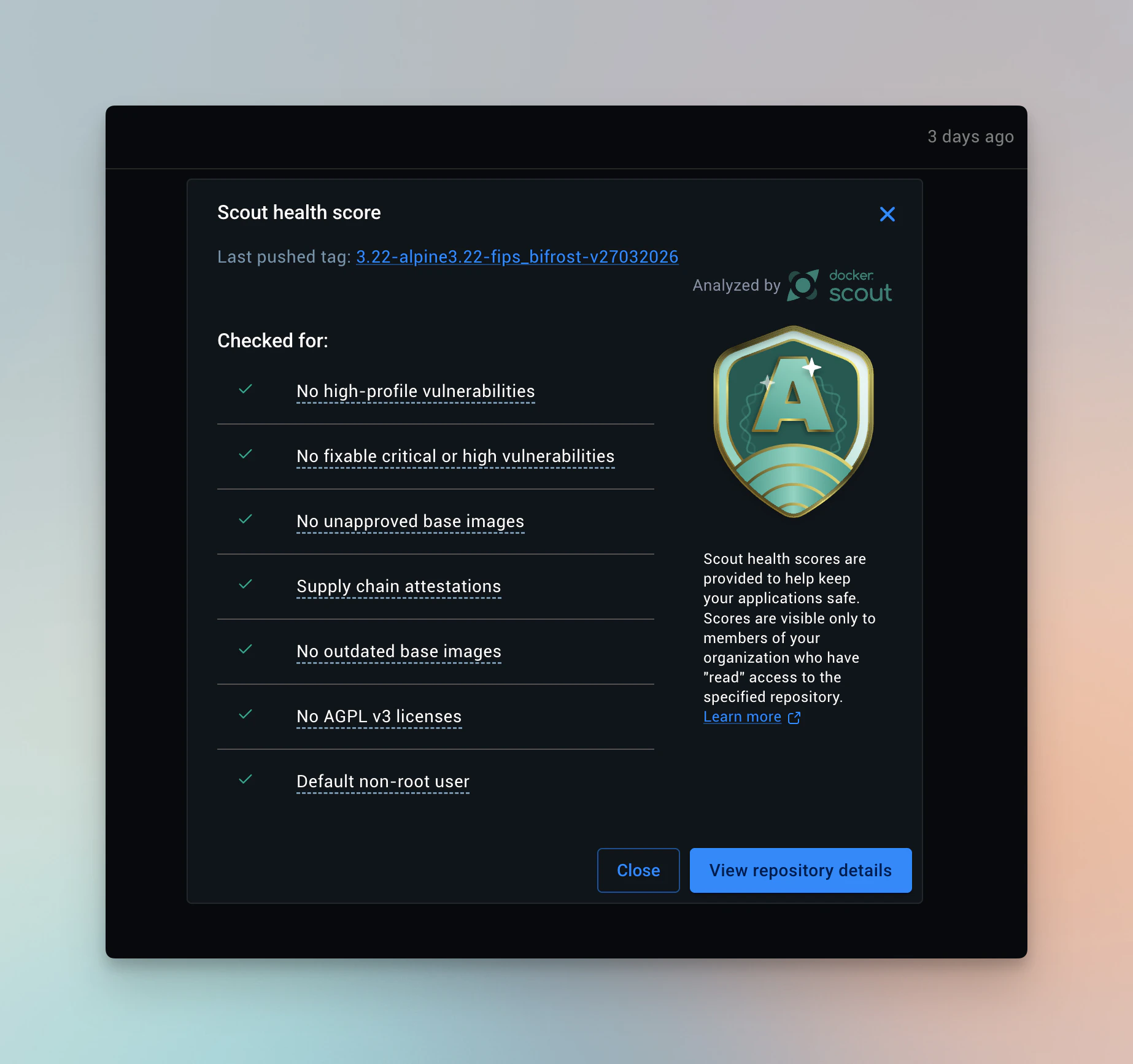
Docker Scout
Docker Scout is enabled at the Docker Hub repository level for themaximhq/bifrost image. Every image pushed to Docker Hub is automatically scanned for CVEs against
continuously updated vulnerability databases.
GCP Artifact Registry Scanning
Enterprise images are pushed to GCP Artifact Registry (and AWS ECR for select environments). GCP Artifact Registry provides built-in vulnerability scanning that automatically analyzes container images for OS and language package vulnerabilities.Supply Chain Security
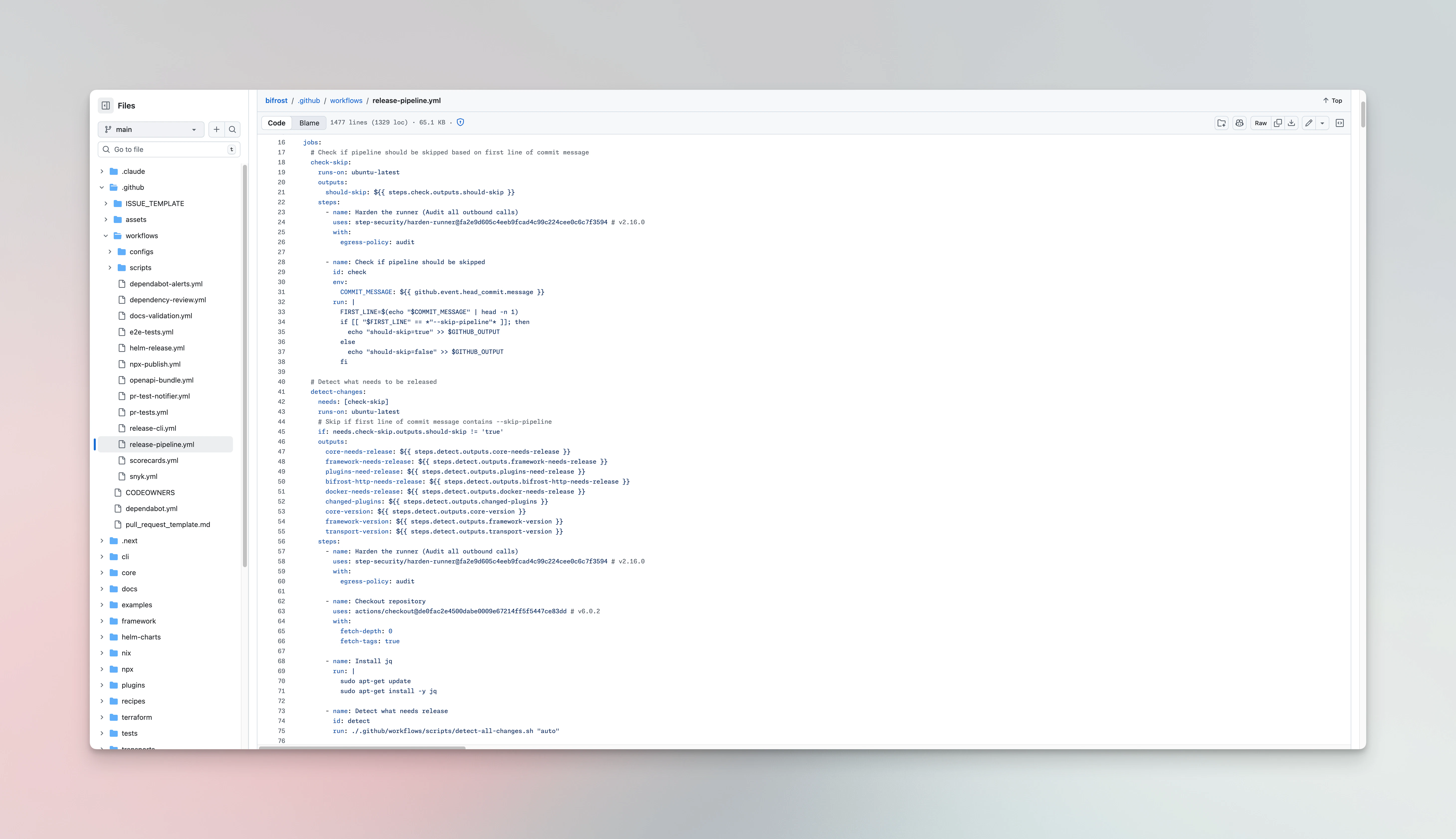
GitHub Actions SHA Pinning
All GitHub Actions in the open-source repository are pinned to exact commit SHAs - not mutable version tags. This prevents supply chain attacks where a compromised action maintainer could push malicious code to an existing tag.| Repository | Pinning Strategy | Actions Pinned |
|---|---|---|
bifrost (OSS) | Full SHA with version comment | 103 / 103 (100 %) |
bifrost-enterprise | Full SHA with version comment | 103 / 103 (100 %) |
NPM Provenance
Published npm packages include SLSA provenance attestations, providing a verifiable link between the published package and its source commit.Dependency Pinning in CI
All language runtimes are pinned to specific versions across CI workflows to ensure reproducible builds and prevent unexpected behavior from runtime updates.| Runtime | Pinned Version | Used For |
|---|---|---|
| Go | 1.26.1 | Core build, tests |
| Node | 25 | UI build, npm packages |
| Python | 3.11 | Integration and governance tests |
| uv | SHA-pinned via astral-sh/setup-uv | Python package management |
uv.lock files for deterministic, reproducible installs:
Dependency Management - Dependabot
Dependabot monitors four ecosystems on a weekly schedule, automatically opening pull requests for outdated or vulnerable dependencies.Go Modules
Covers
/core, /framework, /transports, /plugins/*, and /examples/**npm Packages
Covers
/ui, /npx, and /examples/**Docker Images
Monitors base images in
/transportsGitHub Actions
Tracks action version updates across all workflows
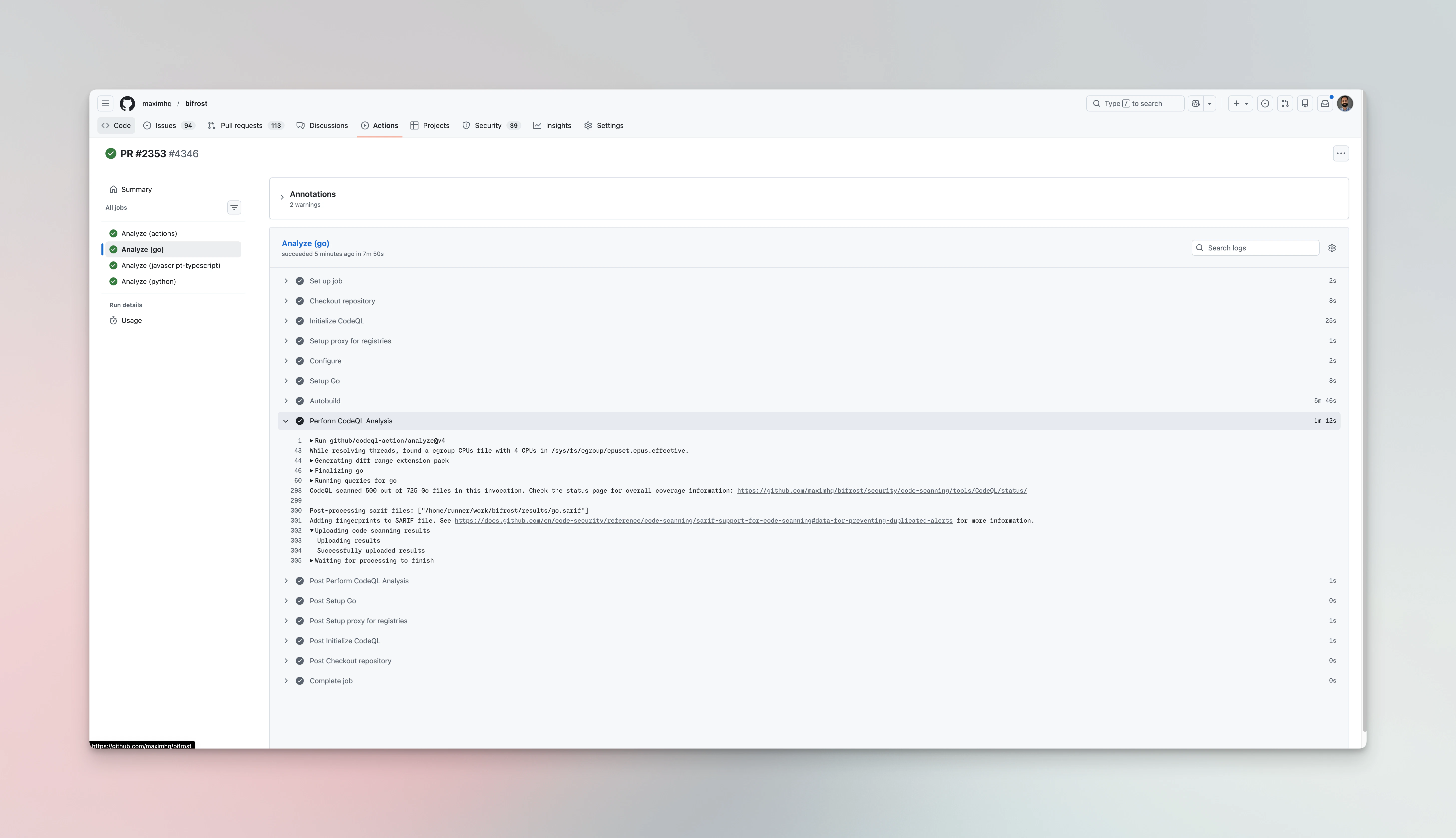
Code Analysis - CodeQL
GitHub’s CodeQL performs semantic code analysis on every push and pull request, complementing Snyk’s SAST coverage with GitHub-native findings.- Analyzes Go and JavaScript/TypeScript codebases
- Detects security vulnerabilities, bugs, and code quality issues using GitHub’s query suites
- Results appear directly in the GitHub Security tab alongside Snyk findings
Workflow & Network Security
Principle of Least Privilege
All GitHub Actions workflows follow the principle of least privilege. Permissions are set at the job level, not the workflow level, and are scoped to the minimum required.| Permission | Granted To | Reason |
|---|---|---|
contents: read | All jobs (default) | Read repository code |
contents: write | Tag creation, releases | Create git tags and releases |
security-events: write | Snyk jobs | Upload SARIF to Security tab |
id-token: write | Cloud auth, npm publish | OIDC federation, npm provenance |
pull-requests: write | PR test reporters | Post test results as PR comments |
Tailscale VPN
Enterprise deployment workflows authenticate through Tailscale before accessing any infrastructure. This ensures that CI/CD runners can only reach deployment targets through an encrypted, identity-aware network - never over the public internet.- OAuth-based authentication - No long-lived API keys; runners authenticate via OAuth client credentials
- Version pinned - Tailscale
1.84.0to prevent unexpected behavior from updates - Tagged runners -
gha-citag enables Tailscale ACL policies scoped to CI/CD access
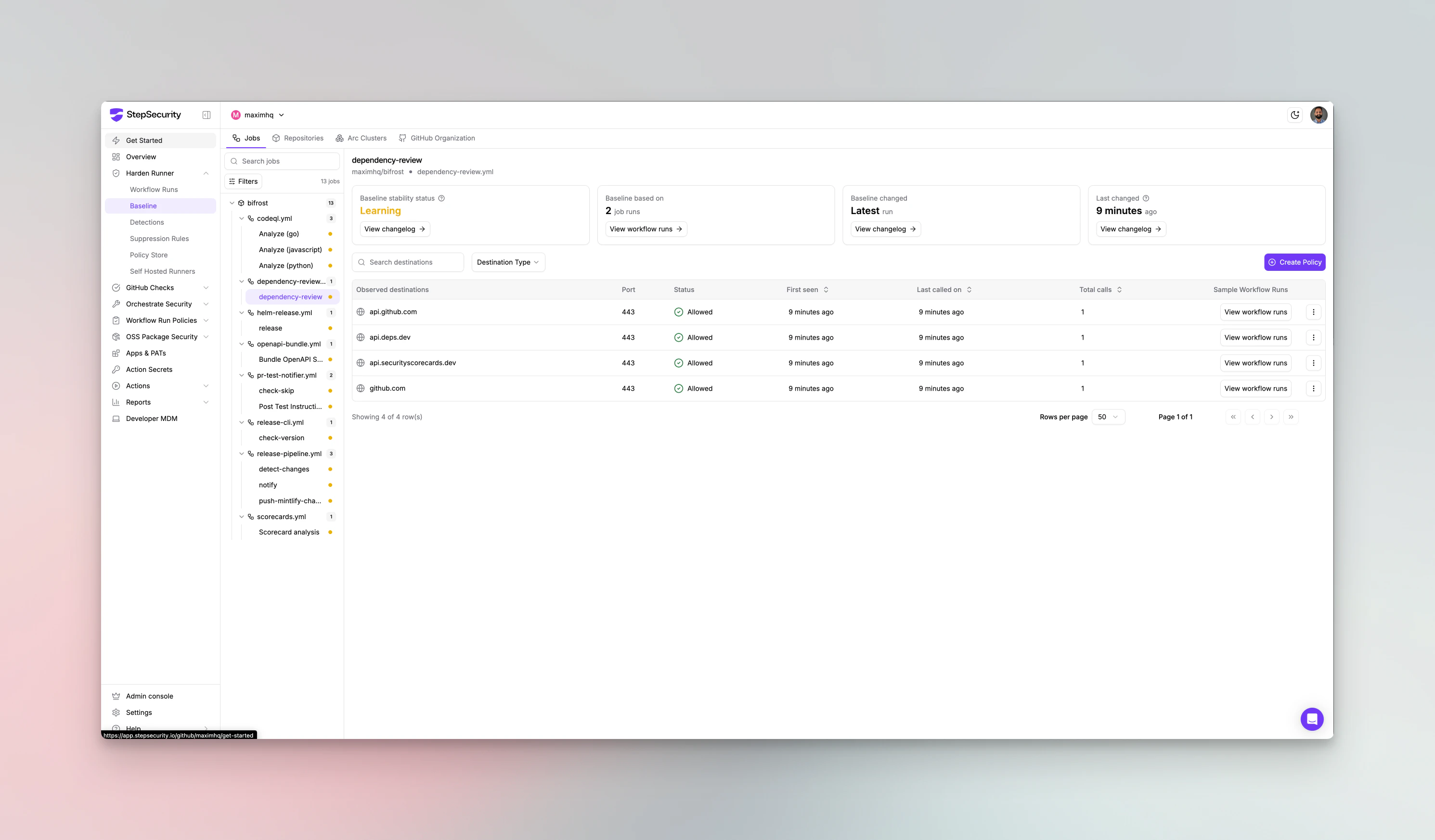
StepSecurity
StepSecurity automatically hardens GitHub Actions workflows by applying security best practices across all CI/CD pipelines.- Adds
permissionsblocks to workflows that are missing them - Pins action versions to full SHAs where mutable tags were used
- Detects insecure patterns like unquoted interpolations and artifact poisoning risks
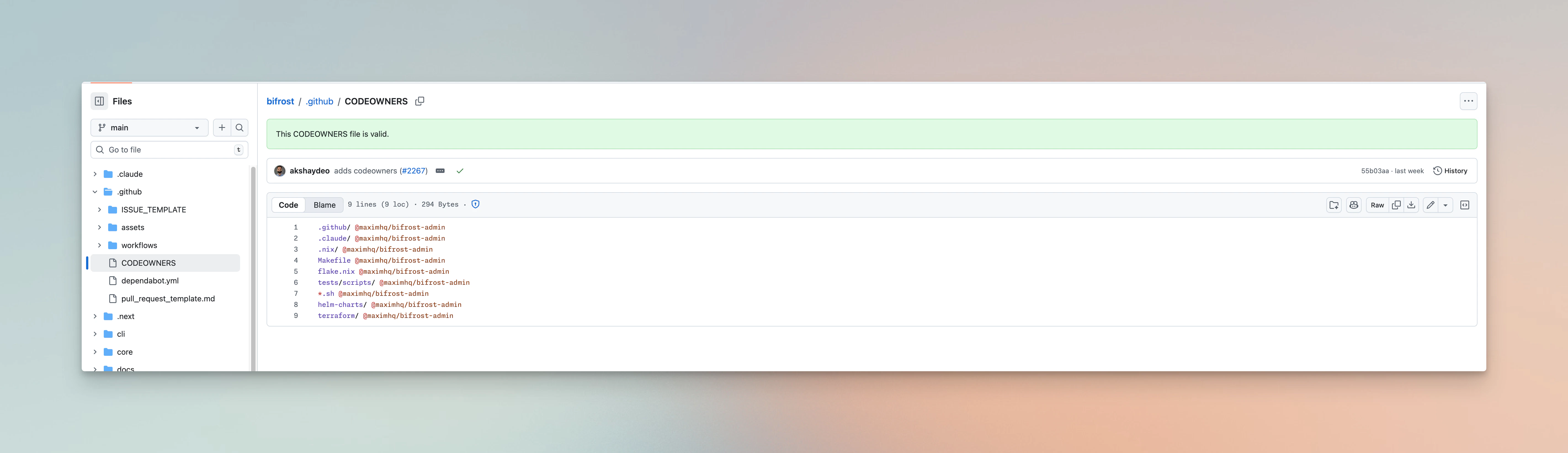
CODEOWNERS
Critical paths in the repository are protected by aCODEOWNERS file, ensuring that changes to
security-sensitive areas require review from designated maintainers before merging.